Quantum cryptography uses the weird laws of physics to secure communications in a way that's more secure than commercial, math-based encryption. But there are fundamental limitations to today's quantum encryption systems that make them expensive and impractical for widespread use.
Toshiba's U.K.-based research lab yesterday announced it has developed a method for deploying quantum cryptography on a network of up to 64 users, overcoming the point-to-point communications quantum systems are limited to now. Researchers published a paper in Nature describing their multi-user architecture, which they say removes one of the main barriers to broader adoption.
Just like conventional encryption systems, quantum cryptography transmits keys from one user to another that allows the receiver to unlock the contents of a message. In a quantum key distribution system, though, the keys are encoded as a stream of photons. A transmitter uses a laser to generate pairs of photons and send them over a fiber optic cable. These twin photons have an opposite polarity—they will oscillate horizontally or vertically, for instance. According to the laws of quantum physics, if someone tries to measure their state, the receiver can detect the eavesdropping and reject the keys.
But these transmissions only work between two points and each user on the network needs a specialized photon detector. Toshiba researchers designed a system to share that expensive detector across multiple users, effectively creating a network hub. In its configuration, a single photon detector is at one end of the network while each end user has a photon transmitter made with off-the-shelf fiber optical components. The signals of multiple end users are combined and transmitted over a single fiber, enabled a one-to-many architecture.
To do this, Toshiba researchers needed to develop a very fast photon detector that can accurately read fast-arriving signals from multiple end users. They also needed to adjust the detector to compensate for changes in temperature that can happen from having multiple users on a single fiber link, which can change its length slightly and could cause errors. The group said they demonstrated the system operating for 12 hours.
Creating a dedicated quantum key distribution network with hub-and-spoke architecture is one way to make technology less expensive. In another effort, research company Battelle is working with quantum key distribution startup ID Quantique to build a hybrid encryption system that sends photons between two points and then uses traditional encryption on a local network. (See, Long-Distance Quantum Cryptography.)
The Toshiba work doesn’t directly address the range limitation of quantum encryption. Because light signals fade, photon transmissions are limited to about 100 kilometers. But because it could use standard equipment, Toshiba’s system helps bring down the cost of quantum encryption, which could make the technology attractive to a broader set of commercial and government customers.
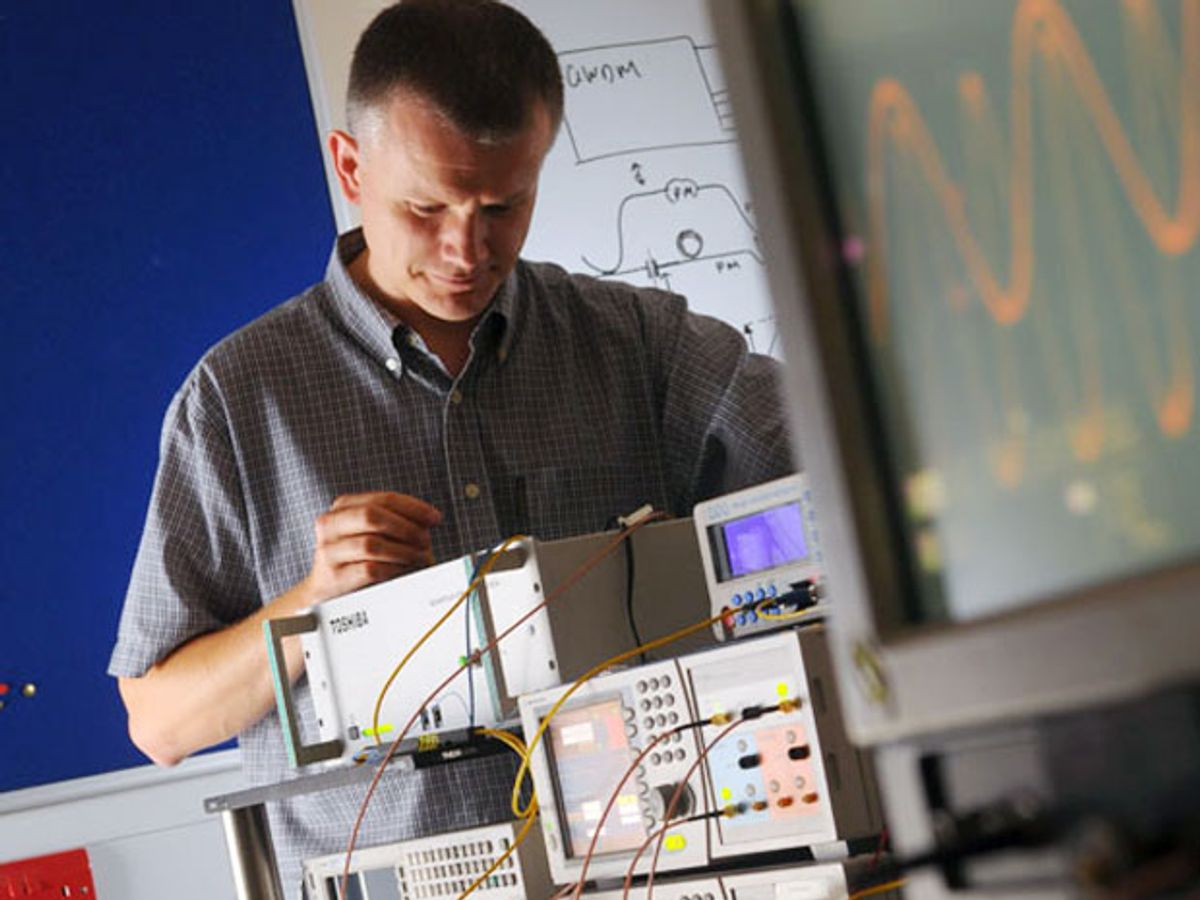
Image: Toshiba