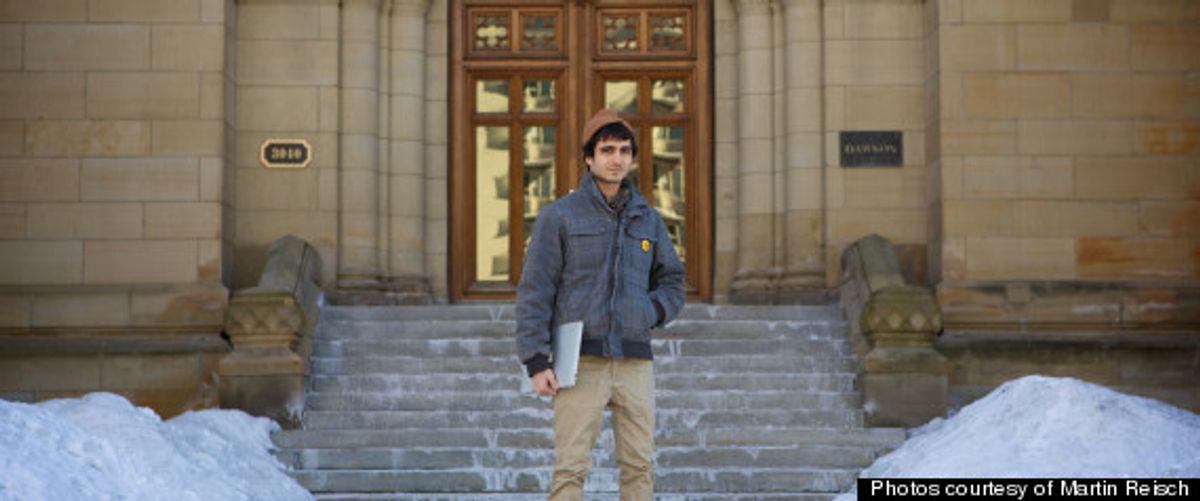
Student Whistleblower Expelled
It was revealed this week that a computer science student in Canada was expelled in November after he discovered a security flaw in his college’s computer system that could have exposed the personal data of more than 250 000 students. Hamed Al-Khabaz and a classmate found the security hole—which would have let anyone querying the system to access every bit of personal information about students contained in the school’s records—while developing an app that would let students access their campus accounts from mobile devices. When Al-Khabaz and his partner reported the problem, Dawson College administrators and officials at Skytech Communications, the company that sold the computer system to the school, initially gave the students a pat on the head for a job well done. But when Al-Khabaz followed up two days later, using a scanning tool to see if the campus and corporate security teams had made good on their promise to fix the vulnerability in Skytech’s Omnivox system, the pat on the head quickly changed to a swift kick in the pants.
Al-Khabaz says that he received a threatening call from Edouard Taza, the president of Skytech, telling him that the scan was illegal and could get him tossed in jail for up to a year. With that threat in the air, Al-Khabaz signed a non-disclosure agreement making him legally bound to keep silent about the security problem, the subsequent scan, the threatening conversation, and the existence of the non-disclosure agreement. Immediately following that episode, Dawson College officials applied their own dose of shoe leather. The school brought him up on charges of “serious professional conduct,” and 14 of 15 computer science professors voted to expel him from the computer science program. Heaped on top of that was the order that he repay grants he received for his studies.
In its defense, the school insists that the press has it all wrong. At a press conference on 22 January—after Al-Khabaz realized that he had very little left to lose by failing to abide by the terms of the non-disclosure agreement and went public with the details of the incident—school officials said the former student had “made an attempt to gain access to a range of systems” and that his activity constituted “a concerted set of attacks on a range of systems.”
An odd twist in the story is that although Dawson College refuses to readmit him, Skytech is one of a number of firms that have offered him a job.
The Downside of Logging Into Everything With One Password
Once again security has been sacrificed on the altar of ease of use. Twitter and Facebook, in an effort to put themselves at the center of Internet users’ online activity, allow their login credentials to be used as a kind of master key for granting access to third-party apps. And right on schedule, the unintended consequences have arrived.
Some apps, designed to automatically read from and write to a Twitter user’s timeline, see who he or she follows, and update the person’s profile, are supposed to do so only if given permission. But according to Cesar Cerrudo, a security researcher at IOActive, he recently discovered a flaw in Twitter’s code that let these third-party apps access Twitter users’ direct messages—which are supposed to be private—even when Twitter users had not agreed to give the apps that level of access.
In the course of testing the functionality of an app—specifically the feature that allows user to sign in with their Twitter credentials—he noticed that the permission level was initially set to allow the user enough access to read existing tweets and post new ones. But after logging out and signing back in a few times, the app began displaying Twitter direct messages. Meanwhile, the application settings page still indicated that the permission level had not been changed.
After unsuccessfully attempting to figure out the nature of the security flaw, Cerrudo notified Twitter’s security team, which promptly fixed the problem. Unfortunately, Cerrudo told Kaspersky Lab’s Threatpost, Twitter did not issue a general alert to its users making them aware of the issue.
U.S. Military Seeks Automated Cyberattack Defense
The U.S. Department of Defense's Advanced Research Project Agency (Darpa), is on the hunt for new ways to scan and analyze the massive amounts of data generated by the computer networks run by government departments. The effort, part of Darpa’s Cyber Targeted-Attack Analyzer program, is designed to "automatically correlate all of a network’s disparate data sources—even those that are as large and complex as those within the DoD — to understand how information is connected as the network grows, shifts and changes," says an agency news release. Keeping an eye on every bit of a network as extensive and complex as that run by the Department of Defense is a tremendous undertaking. The security and performance-monitoring systems attached to the networks collect untold haystacks of data on a daily basis. Darpa is hoping that employing a new, automated approach will make ferreting out the occasional needle easier. “The Cyber Targeted-Attack Analyzer program relies on a new approach to security, seeking to quickly understand the interconnections of the systems within a network without a human having to direct it,” Richard Guidorizzi, manager of the program told Kaspersky Lab’s Threatpost. “Cyber defenders should then be capable of more quickly discovering attacks hidden in normal activities,” he said.
The program comes on the heels of the U.S. military issuing several solicitations for offensive cyberwarfare capabilities.
Google Back as Sponsor of Hack-a-lympics
The Pwn2Own hacking contest is back—this year with new rules and a bigger cache of prize money courtesy of Google. HP TippingPoint, organizer of the annual event, says the hacker games—which will take place between 6 and 8 March at the CanSecWest security conference in Vancouver, British Columbia—will test entrants’ ability to demonstrate new exploits taking advantage of vulnerabilities in the Chrome, Firefox, Internet Explorer or Safari browsers, or the Adobe Reader, Adobe Flash or Oracle Java browser plug-ins. Big money (US $100 000) will go to the person who hacks Chrome on Windows 7 or Internet Explorer 10 on Windows 8 in the fastest time. The quickest to break into IE9 will get $75 000; the prizes go down from there, to $20 000 for an exploit for Java, which has taken a public beating for its security failings.
Google’s sponsorship is worthy of note, says Computer World, because the search company backed out underwriting the event last year over a disagreement with regard to the rules. Unlike last year, Pwn2Own participants must reveal the full exploits and all the details of the vulnerability used in their attacks. Google was upset that the contests wouldn’t result in vendors having the ability to see and fix the flaws. But it didn’t simply take its ball and go home. It put on a $120 000 Chrome-specific hacker contest at CanSecWest. Google has already confirmed that it will present Pwnium again this year. But the search firm has yet to reveal whether it will take place at CanSecWest.
Willie Jones is an associate editor at IEEE Spectrum. In addition to editing and planning daily coverage, he manages several of Spectrum's newsletters and contributes regularly to the monthly Big Picture section that appears in the print edition.