First: Do No Harm. Second: Keep Others From Doing It.
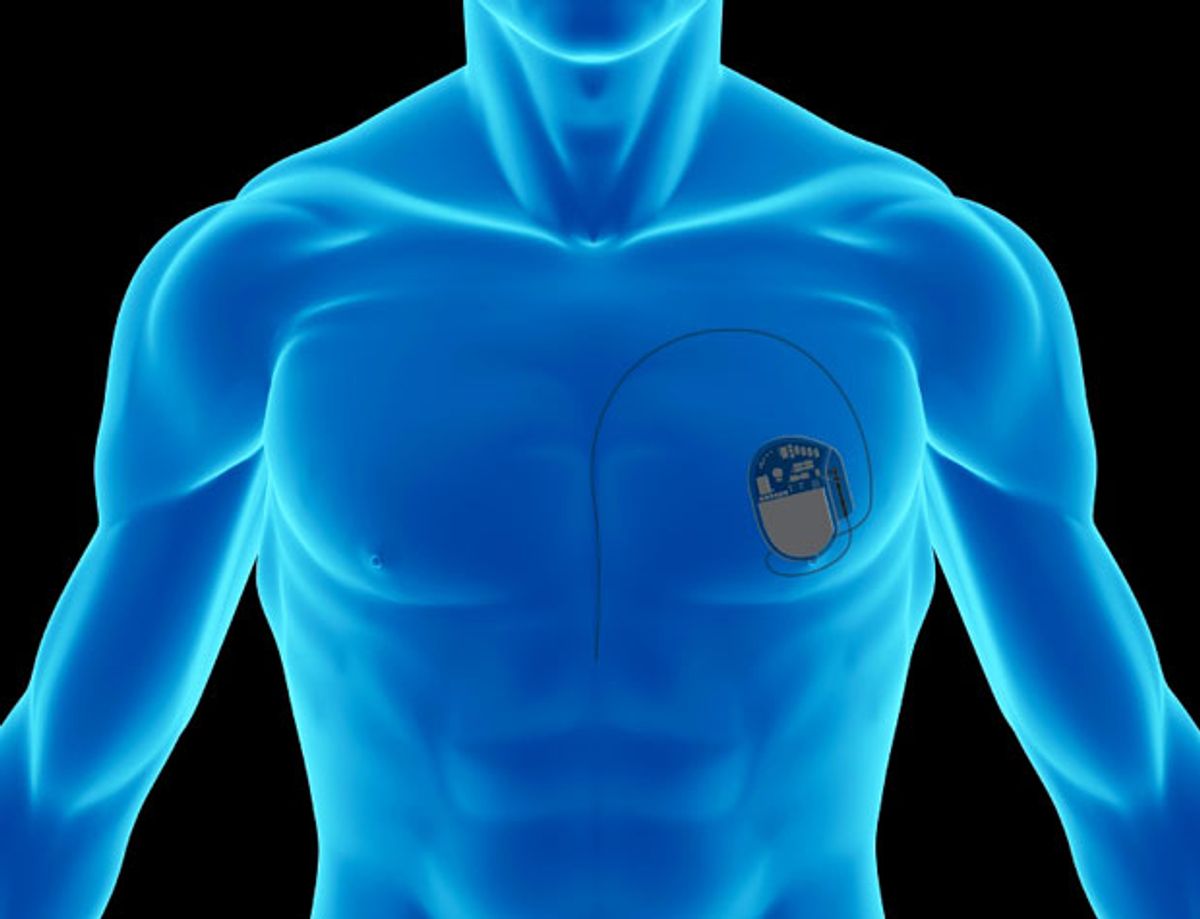
In the wake of discoveries that some medical devices are vulnerable to remote tampering via the Internet, the U.S. Food and Drug Administration (FDA) issued new guidelines this week that are meant to direct medical device manufacturers in beefing up security. The hope is that we'll never have to read about—or worse, personally experience—death or injury because some malware-infected gadget didn't work the way it should.
The FDA recommendations call for device makers to review their cybersecurity practices and test their products with an eye toward ensuring that their authentication setups can limit access to authorized users only. The guidelines also urge health care facilities to be more vigilant in updating their antivirus software, to set stricter controls on who accesses their networks, and to cooperate with device makers to investigate and fix security breaches.
The FDA says that although no deaths or injuries associated with these vulnerabilities or malfunctions have been reported, the rise in cybercrime makes such an outcome “increasingly likely.” The guidelines, though not legally enforceable, put device makers and medical facilities on notice that they need to step up their efforts to keep diagnostic machines from being taken over by attackers, prevent pacemakers from being reset so that they deliver fatal shocks, and to keep insulin pumps from being tampered with.
The FDA action was prompted by the U.S. Government Accountability Office, which asked it to “develop and implement a plan expanding its focus on information security risks.” It’s about time. Just imagine someone undergoing a surgical procedure where an advanced robot is doing the cutting as proxy for a surgeon in another part of the world. Malware in the system that controls a mechanical arm—or a man-in-the-middle-attack—could be deadly. And even banal mash-ups of technology and medicine could put patients at risk. Computerized drug dispensaries, meant to keep people from receiving the wrong prescription or the wrong dose, could be targets.
Online Bank Robbers Rounded Up
Federal prosecutors in the United States arrested and charged eight members of a Ukrainian cybercrime ring with conspiracy, wire fraud, money laundering, and identity theft this week. The federal complaint (pdf) says they stole more than $15 million from financial institutions such as Citibank, JP Morgan Chase, TD Ameritrade and PayPal. The group also ripped off the U.S. military, making Department of Defense Finance and Accounting Service one of its victims.
The cybercrime gang specialized in fraudulently obtaining customer account information and using it to transfer money from accounts at 15 different payment processors, banks, and online brokers to prepaid debit cards. They would subsequently have roving teams of “cashers” hit ATMs to withdraw cash or make purchases with the ill-gotten loot. The “Sharapka Cash Out” operation, so named because its mastermind was Oleksiy Sharapka, went on from March 2012 until this week. But Sharapka was not among those rounded up. He was deported to the Ukraine in early 2012—after serving more than 8 years in a U.S. prison—and launched the operation from there.
And in Other Cybercrime News…
Enterprising cybercrooks have used their used their skill at manipulating online transmissions to recruit job seekers looking for work at CareerBuilder.com, a legitimate job site. When a job hunter with a machine infected with the Zeus Trojan navigates to the site, Zeus injects code that adds links to supposedly real job offers. But Researchers at Trusteer say the links diverted users to a third-party site that attempts to lure them into becoming money mules (similar to the “cashers” in the previous item) for an organized cybercrime operation.
The “NetTraveler” cyberespionage campaign claimed more than 350 high-profile victims from more than 40 countries during an eight-year run. The malware stole documents, including Microsoft Word files, PowerPoint presentations, and Excel spreadsheets while engaging in continuing computer surveillance. Computerworld says that, in a report detailing how NetTraveler stole so much data and remained undetected for so long, researchers at Kaspersky Labs surmised that group behind the campaign “has around 50 members, most of whom are native speakers of Chinese and have some knowledge of English.”
A malware-laced knockoff version of the popular Android app Bad Piggies slipped through the security filters at Google Play app store in late May and was downloaded more than 10 000 times before security researchers at F-Secure spotted it on Wednesday. The app, called “Bad Pigs,” set the table for stealing data by asking users for permission to change settings, then gorged itself on users’ personal information.
Photo:Max Delson Martins Santos/iStockphoto
Willie Jones is an associate editor at IEEE Spectrum. In addition to editing and planning daily coverage, he manages several of Spectrum's newsletters and contributes regularly to the monthly Big Picture section that appears in the print edition.