One car loaded with malware could someday infect hundreds or thousands of other vehicles at the local car dealership or auto repair shop. To prevent that “auto brothel” scenario, a security researcher recently presented a $20 tool designed to reveal security flaws in the testing equipment commonly used to update car software or check vehicle systems.
The dangerous scenario for modern drivers was presented during a talk at the Derbycon hacker conference held in Louisville, Kentucky, last week, according to Wired. A hacker could theoretically bring in an infected vehicle for service with the aim of spreading malware to the testing equipment used by mechanics and dealerships, said Craig Smith, a security consultant and author of the Car Hacker’s Handbook. The infected equipment could spread the malware to other customers’ vehicles and possibly compromise electronically-controlled systems such as steering or braking.
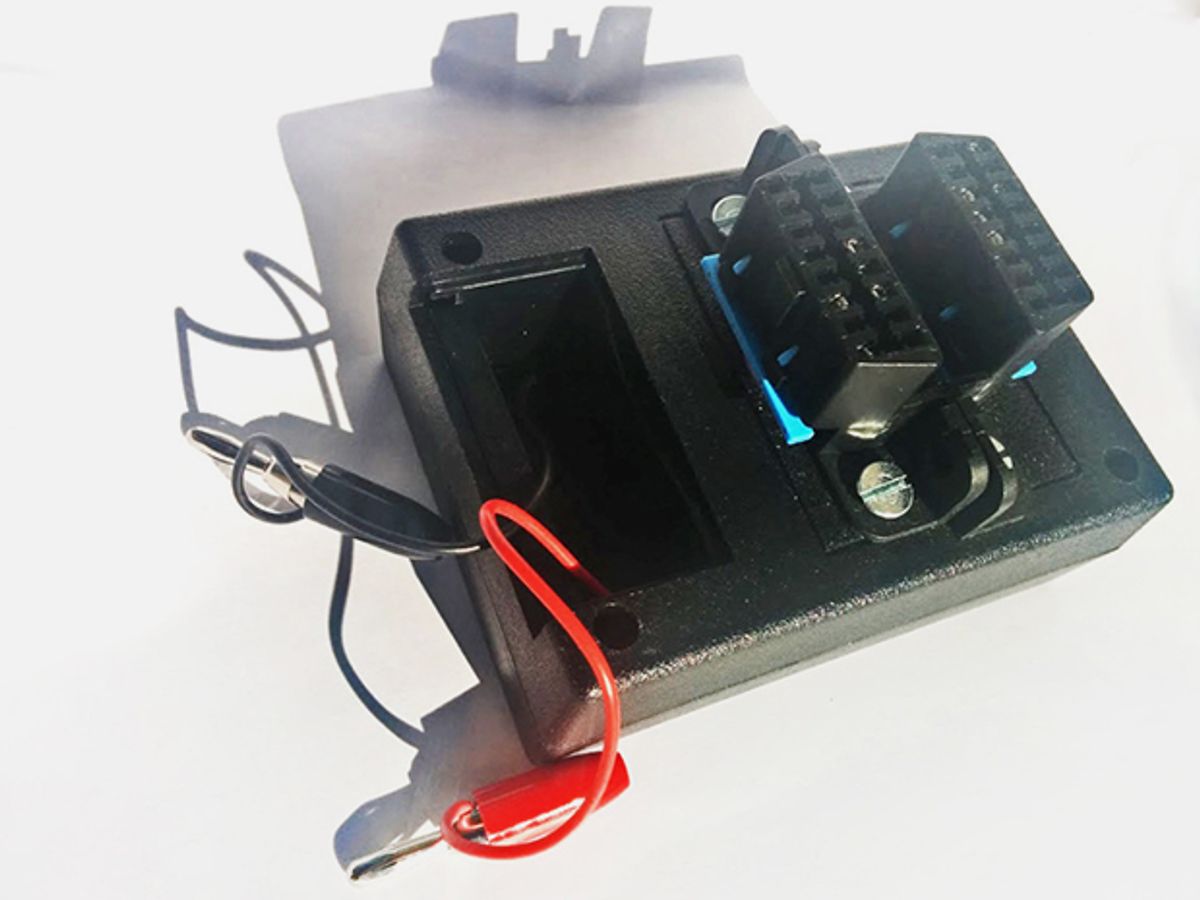
Smith created a tool that mimics how a malware-carrying car might try to infect a dealership’s testing equipment. The hardware consists of On-board Diagnostic ports similar to the ones that mechanics would plug their diagnostic tools into for access to the car’s CAN network. (CAN typically connects the car’s central computer to its various electronic subsystems.) The tool’s software tests the diagnostic tool with random data until it causes glitches that may represent security holes to exploit.
Past security exploit demonstrations have shown how vulnerable modern cars, with all their electronic systems, have already become. During the 2015 Blackhat computer-security conference, researchers explained how they simply relied on an Internet connection to hack the entertainment system of a 2014 Jeep Cherokee. They eventually also accessed the vehicle’s CAN network and gained control over everything from steering to braking.
Such potential security threats will likely only increase in the future as new cars increasingly rely upon more electronic systems. The possible deployment of self-driving robot cars, with their additional suites of sensors and systems, may also further complicate the picture. For example, recent research has shown how to hack the laser-ranging systems used by most robot cars to detect road obstacles.
But by focusing on car dealerships, Smith hopes to draw attention to a previously overlooked security concern. After all, the only thing that might be worse than having a few infected cars is a situation where the places drivers take their vehicles for repairs become the source of infections that spread to thousands of cars. Security audits of dealerships’ testing equipment could represent a step toward better security for all drivers.
Jeremy Hsu has been working as a science and technology journalist in New York City since 2008. He has written on subjects as diverse as supercomputing and wearable electronics for IEEE Spectrum. When he’s not trying to wrap his head around the latest quantum computing news for Spectrum, he also contributes to a variety of publications such as Scientific American, Discover, Popular Science, and others. He is a graduate of New York University’s Science, Health & Environmental Reporting Program.