My editor at IEEE Spectrum is convinced that in the future smartphones will have spectrometers to probe the world around them [True-Ed.]. As an experimental preview into this era, he obtained a spectrometer with a higher resolution than budget-minded makers have access to today, the Hamamatsu C12880MA, available in small quantities as a US $350 breakout board on Tindie. My part of the experiment? To see what idea the device would spark in me for a consumer-focused application.
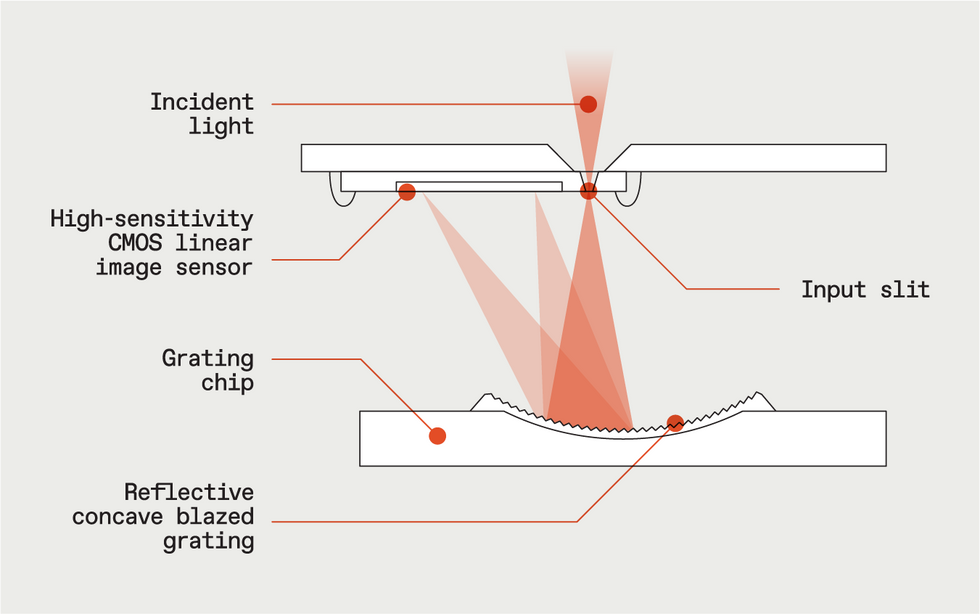
As a bit of background, this spectrometer measures largely visible wavelengths of light and some in the infrared. It breaks out the light into a spectrum of varying intensity, which tells us more about a substance than we’d be able to sense by eyesight (or camera sight) alone. It has 288 individual pixels, which together can sense wavelengths of between 340 to 850 nanometers, with a resolution of 15 nm. This allows for much finer discrimination of spectra than you’d get from a typical $16 maker-grade spectrometer, sensitive to only nine distinct frequency bands.
So how might a smartphone use a spectrometer? What if it could be used to unlock the phone by scanning, say, one’s skin tone—or rather, personal spectral signature? As of now though, the spectrometer—at 20.1 by 12.5 by 10.1 millimeters—is quite small, but not quite appropriate for today’s ultrathin handsets. So I decided to prototype my phone idea by making a password-entry device for my laptop PC that would unlock it when I held my arm up to the sensor.
For my prototype, I plugged the spectrometer breakout board into a small breadboard, along with a Start button and the extremely capable Arm Cortex–based Teensy 4.0. The makers of the breakout board had already tested it with a Teensy, and the Teensy also has the advantage of having built-in USB HID (human interface device) capabilities, allowing it to emulate a keyboard when plugged into a computer.
The plan was that once the button is pressed, the Teensy would trigger an LED on the spectrometer breakout to provide consistent illumination. It would then read and parse the output from the spectrometer. If the spectrum matched that of a previously registered object, the Teensy would then automatically “type” my password, granting access to the computer.
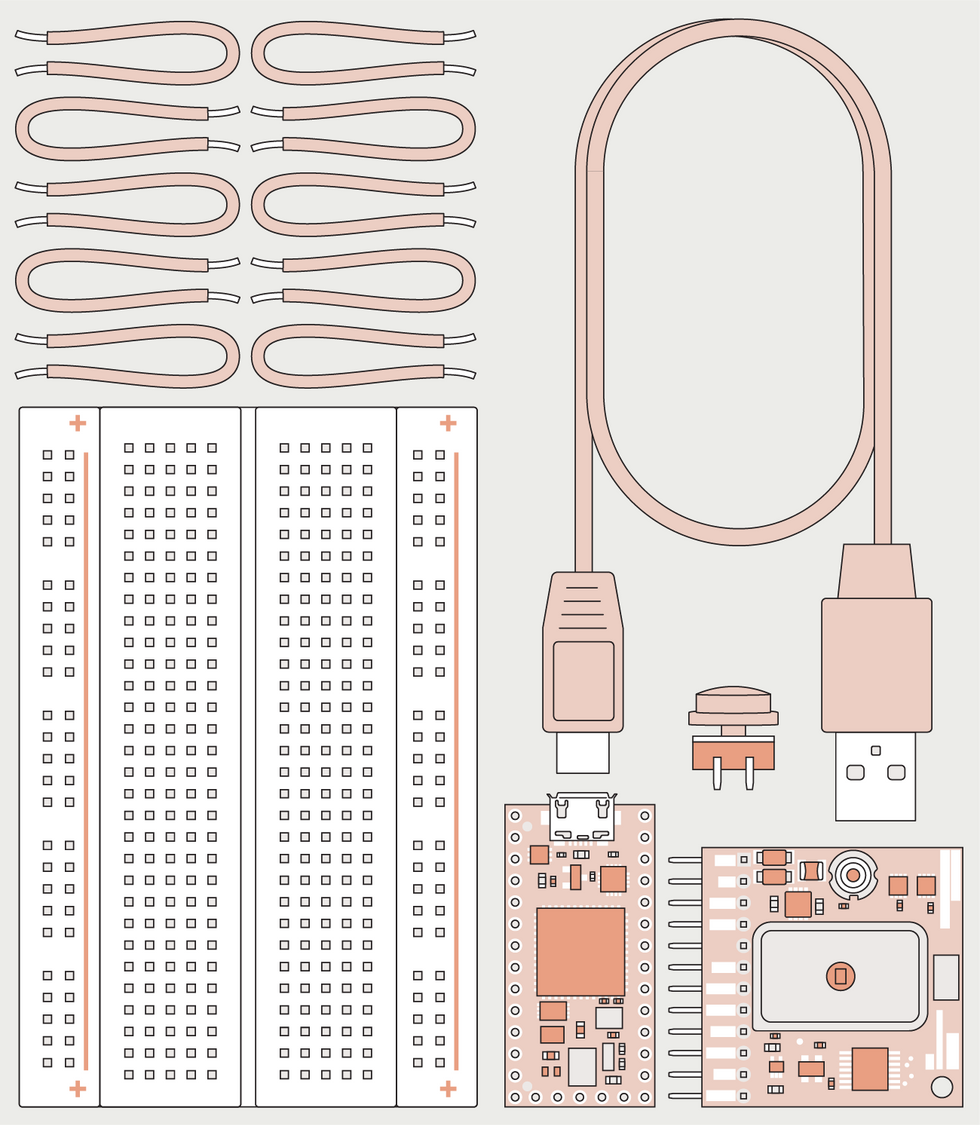
Once I’d tested my sensor/microcontroller setup via the example code found online, the next question was whether or not such a device could send a string of text and actually be granted access to my MacBook computer. This actually turned out to be quite simple with the Teensy board, demonstrated via code from the USB_Keyboard Buttons example provided by the manufacturer of the Teensy. By modifying the text output initiated after a button press, it can send a stored password. Using Keyboard.println normally advances to the next line after text is entered, but it also duplicated the effect of pressing the Enter key in the password-entry box.
Now I needed to set things up so that the password was sent only when wavelength readings from the spectrometer matched up to the correct spectral signature.
I soon realized skin tone wasn’t a good idea. Bodies are irregular, making consistent illumination hard, and many people have a similar skin tone to others. And what if I were to measure my skin after too much sun exposure, drinking a lot of water, or other conditions that could alter it’s signature? These were complications that I wasn’t keen on dealing with, though they might be trivial for a multibillion-dollar phone manufacturer.
For my prototype, I needed an inanimate object to act as a token instead. Something flat that could be positioned at a set distance to the sensor to return consistent spectral intensities, and possessing a distinctive color. It would also have to be something I’d consistently have on my person... Yes, I’m describing using a cellphone cover as the password object, turning the concept of security for your phone on its head.
With the cover at a distance of roughly 40 mm from the sensor, I started taking readings to determine its spectral signature. But the readings were inconsistent, especially just after the phone cover was initially presented to the sensor aperture. The solution was to take multiple readings back-to-back, throw out the first four, and use the fifth as the actual input.
Looking at the results, I realized I didn’t need to try to analyze and compare the entire spectrum. I could pick two notable peaks, and look at the intensities there. So I averaged the output from pixels 50 to 55, along with pixels 150 to 155. The results centered around an intensity count of 495 for the first peak and 315 for the second, based on an integration time of a few microseconds.
Of course, it would be very rare for the measured spectrum of the cover to produce intensities counts that were both exactly 495 and 315, so I was caught in the classic security conundrum—how much leeway did I allow to prevent false-negative lockouts without making the setting so lax I would get false-positive access from incorrect objects? Eventually, with some trial and error, I settled on plus or minus 20 points. Now, when the button is pressed, a spectral reading is taken, compared, and if both values are within range, it enters the programmed password. (I should also note that if you happen to have a word processor or other text editor open and trigger the device, your password would be typed in to be on display for all to see!)
Code for this device is found in my Github repository, which is a modified version of the example code I referred to earlier. My setup should be fairly easy to duplicate and put into a permanent housing, though the spectrometer is admittedly pricey. Until, at least, Samsung or Apple starts churning spectrometers out by the million.
This article appears in the January 2022 print issue as “My Password Is: [Color Bar].”



