In November of 2008, the US Department of Defense (DoD) military and civilian personnel were informed that DoD had immediately suspended their use of USB and removable media devices, including digital cameras, switches, special data entry devices, personal digital assistants (PDA), hand held computers, printers, network hardware, and removable hard data storage devices (USB memory sticks, cards, etc).
Speculation at the time was that DoD's networks suffered a massive hybrid worm/virus attack and that the attack originated in a USB type storage device and could also be spread by them, hence the ban.
According to news reports today, an article to be released later today by Foreign Affairs discussing DoD's cyber strategy confirms the speculation. This Washington Post story states that "Deputy Defense Secretary William J. Lynn III says malicious code placed on the drive by a foreign intelligence agency uploaded itself onto a network run by the U.S. military's Central Command."
Secretary Lynn writes in the Foreign Affairs article that:
"That code spread undetected on both classified and unclassified systems, establishing what amounted to a digital beachhead, from which data could be transferred to servers under foreign control... It was a network administrator's worst fear: a rogue program operating silently, poised to deliver operational plans into the hands of an unknown adversary."
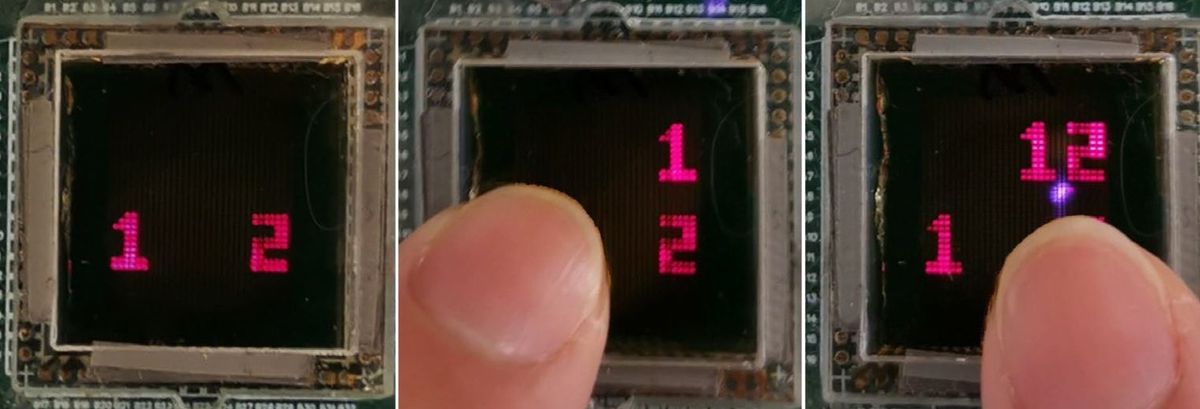
Lynn also says that the DoD has found counterfeit hardware in systems that it has bought.
The Post story says that Secretary Lynn's article discusses in more detail DoD's approach to cyber security, which it calls "active defense."
The Post story also notes that some cyber security experts are concerned that the article will provide "adversaries useful information."
Exactly how escapes me.
Robert N. Charette is a Contributing Editor to IEEE Spectrum and an acknowledged international authority on information technology and systems risk management. A self-described “risk ecologist,” he is interested in the intersections of business, political, technological, and societal risks. Charette is an award-winning author of multiple books and numerous articles on the subjects of risk management, project and program management, innovation, and entrepreneurship. A Life Senior Member of the IEEE, Charette was a recipient of the IEEE Computer Society’s Golden Core Award in 2008.