Willie Sutton famously said that he robbed banks because that's where the money was. You might think that today's thieves would do the same, possibly by hacking into ATM machines. Yet it turns out that financial services account for only 14 percent of data breaches, while 20 percent are in the food and beverage industry.
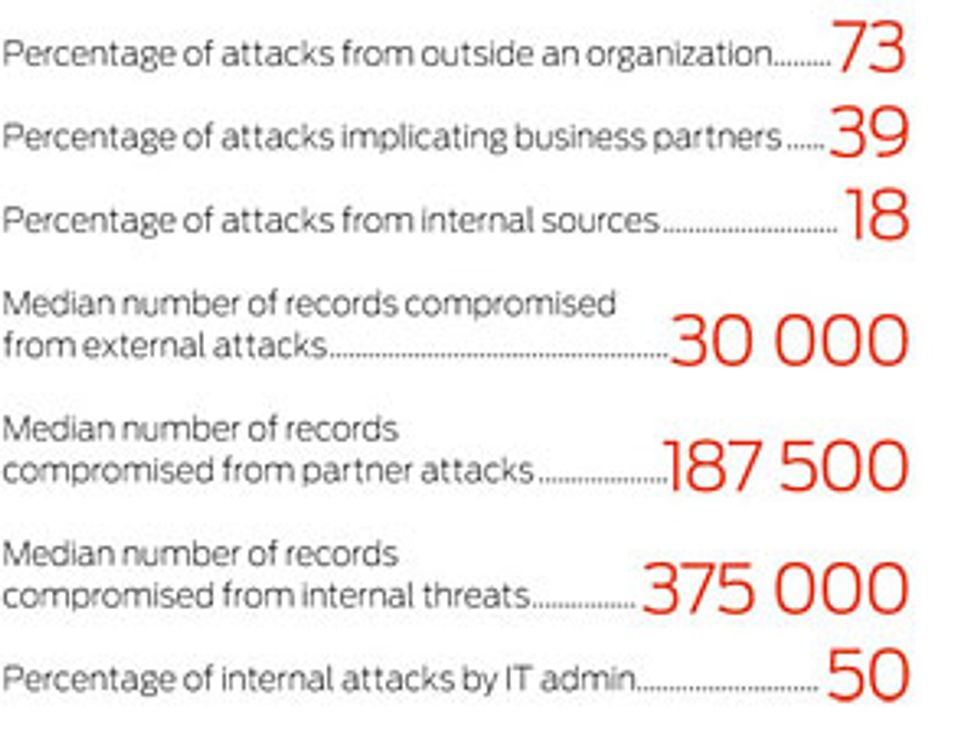
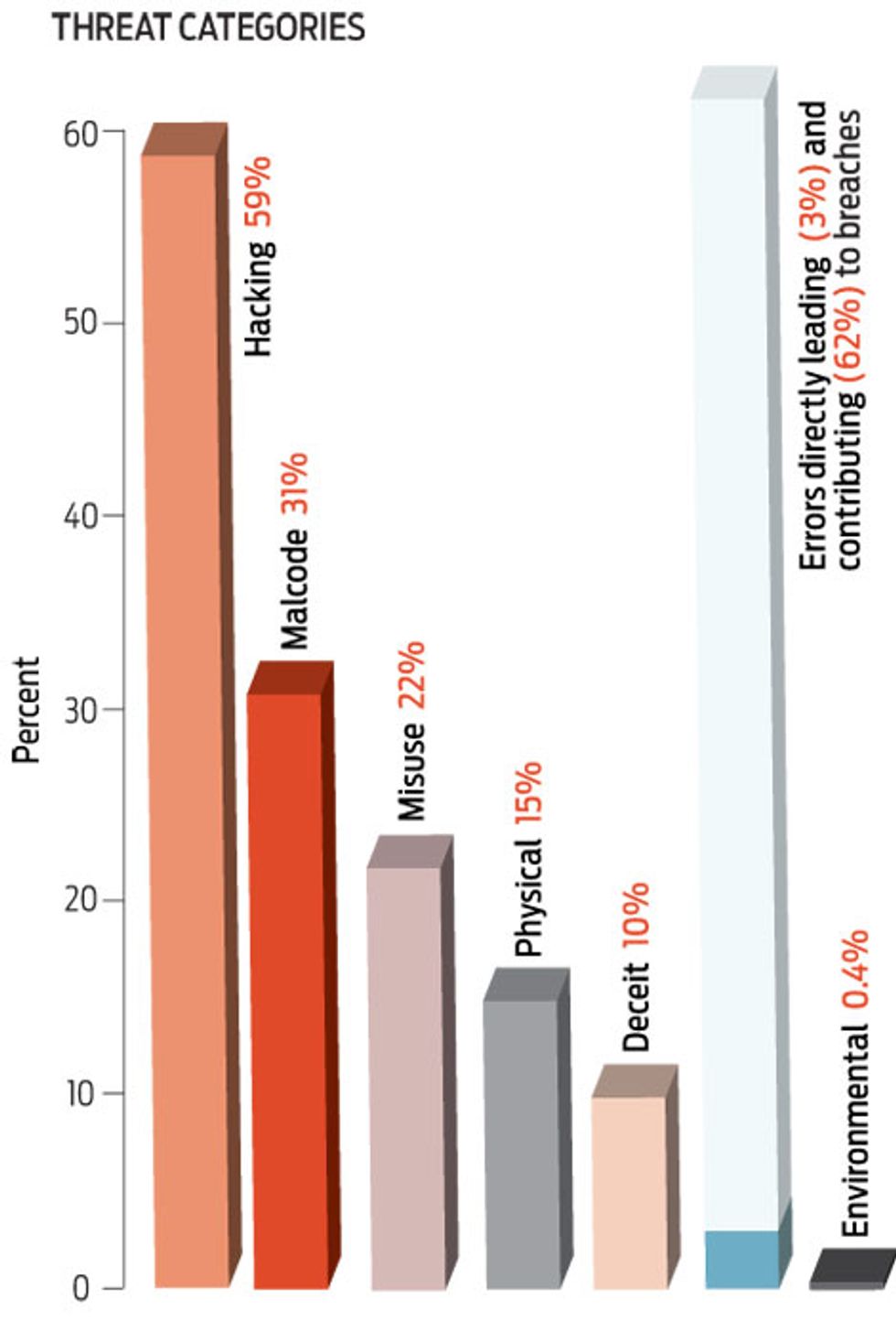
That's just one surprising statistic in a new global study of some 500 security breaches handled by Verizon Business's RISK Team between 2004 and 2007, involving more than 230 million data records. Verizon's report sorts attacks into seven categories. Hacking is, unsurprisingly, a cybercriminal's favorite weapon. Errors, such as incorrect network settings, directly led to just 3 percent of the breaches, but by giving bad guys a leg up they ended up contributing to many more.
In a disturbing trend, in the study's first year only 8 percent of all attacks involved partner organizations, such as vendors and customers, but by 2007 fully 44 percent did. Twentyâ''four percent of all attacks originating outside an organization came from IP addresses in Eastern Europe. Such addresses can't always lead to a particular attacker's exact location, but some clear patterns emerge. For example, attacks on point-of-sale systems were frequently traced back to Eastern Europe and Russia, while Web graffiti and other defacements often originated in the Middle East.
The full report is available at https://www.verizonbusiness.com/resources/security/databreachreport.pdf.
To Probe Further
For more on insider cyberattacks, see ”Data Theft by Partner Companies on the Rise.”