18 December 2012—A vulnerability inside all current Cisco IP phones [PDF]—one of the top selling brands of voice over Internet Protocol telephones—allows hackers to take complete control of the devices, according to computer scientists at Columbia University.
“Once in, the attacker can use the phone’s microphones to stealthily exfiltrate audio data at any time, regardless of whether a phone call is in progress,” says Ang Cui, one of the Columbia computer scientists who discovered the vulnerability. The hacked phone can then infect other phones on the same network and attack connected computers and devices such as printers, he adds.
The Columbia researchers reported the vulnerability to Cisco on 22 October, within a few days of discovering and verifying the bug. The company has produced a patch, but it’s unclear how many phones are still vulnerable.
“We could turn a phone into a walkie-talkie that was always on by rewriting its software with 900 bytes of code. Within 10 minutes, it could then go on to compromise every other phone on its network so that you could hear everything,” Cui says.
Cisco makes phones that are used by the U.S. federal government, the financial sector, and many large private enterprises, Cui points out. [Editor’s note: We use Cisco IP phones here at IEEE Spectrum, too.] Michael Costello, another Columbia computer scientist, used Google to find photos of Cisco phones in the White House, Air Force One, a national laboratory, and in former CIA director David Petraeus’s office. “Having a vulnerability in a phone like this gives you ears in many skyscrapers in cities around the world,” Cui says.
Cisco phones run operating systems based on Unix. The researchers found “very exploitable bugs” in the phone’s operating system kernel—the heart of the OS, responsible for controlling all other programs in a computer. The bug can give intruders total access to the phones, Cui says.
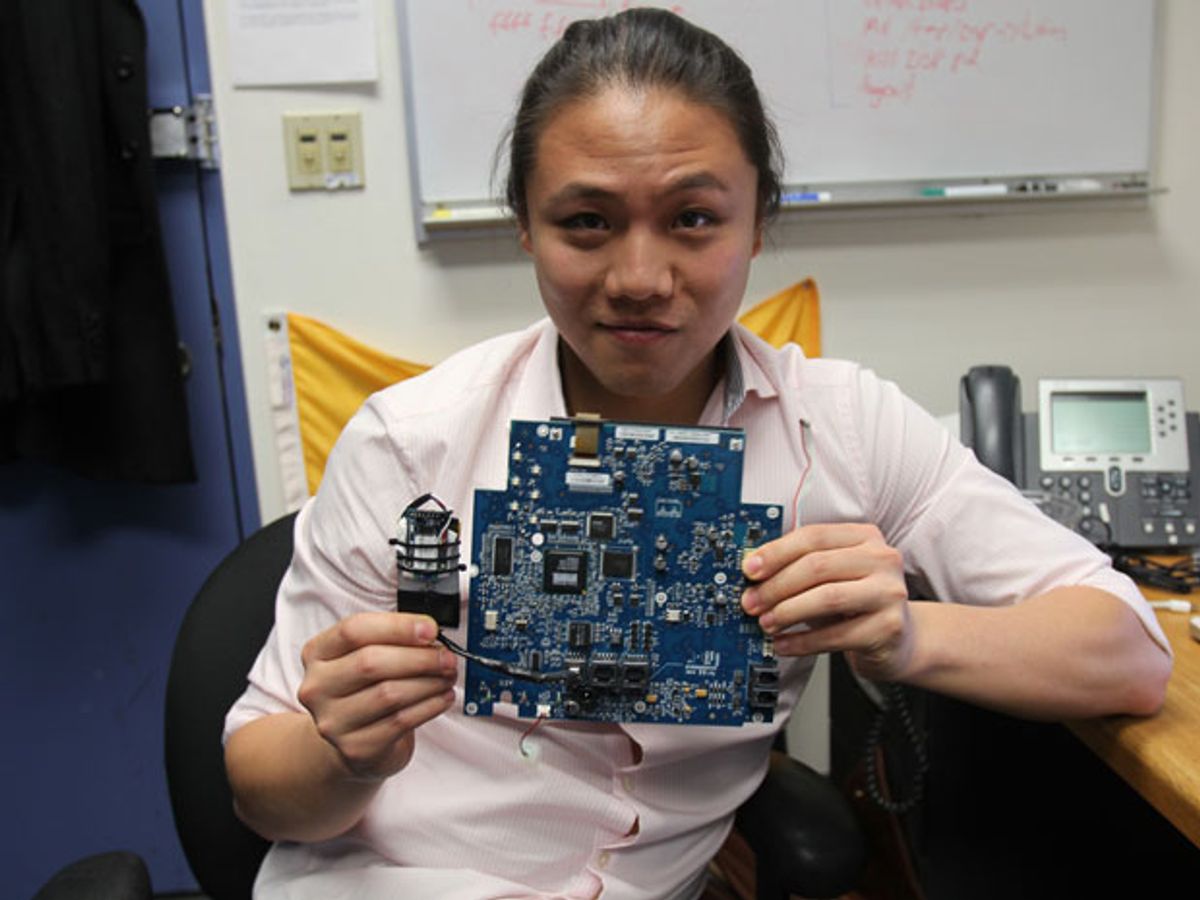
The researchers developed a device they call “the Thingp3wn3r,” which can attach to a phone and connect the phone via Bluetooth to an intruder—say, a hacker using a specialized smartphone app.
Although the attack the researchers developed relies on physical access to the target telephone, Cui says they could also remotely compromise Cisco phones over the Internet. He and his colleagues plan to detail that work at the Chaos Communication Congress in Hamburg, Germany, on 27 December. The researchers discovered this vulnerability as part of their study of embedded computers, the electronics that, among other things, run power plants, printers, prison cell doors, and insulin pumps.
“I’d say this exploit is a poster child for the sad state of embedded security,” says Kurt Stammberger, vice president of market development at the security technology company Mocana, in San Francisco, who did not take part in this research. “Embedded devices, generally speaking, are very poorly secured, if they are secured at all.
“As everything connects, the problem is getting more serious because of the pervasiveness of these devices and the critical role that many of these devices play,” Stammberger says. “The scary part is, we depend on these poorly defended devices in contexts that are often more critical than those in which PCs work—to deliver drugs to us in metered intravenous doses in the hospital, or manage current and voltage across power grids worldwide, or throttle pumps and release valves at chemical plants.”
Regarding the Columbia hack, a Cisco spokesperson says the company has “developed workarounds and a software patch to address this vulnerability, and we are working to validate these with our engineering teams and the [Columbia] researchers.” Cisco says that once the final patch is consolidated, it will be incorporated into its next major software release, perhaps early next year.
Although Cisco’s patch can guard against any future infections via Thingp3wn3r, it is no guarantee against any malware that intruders may have already inserted into the phones. In principle, such malware could override the patch and make the phone vulnerable all over again, Cui says. He and his colleagues at their start-up, Red Balloon Security, are developing programs they call “ symbiotes,” which reside on embedded computers and can detect and defend against such intrusions. “We were able to discover this vulnerability as a consequence of our symbiote research. It’s hard to say who else already knew about this vulnerability,” he says.
Cisco put together its patch for the vulnerability on 20 November, and Cui and his colleagues detailed their findings at the Amphion Forum in San Francisco on 5 December. [PDF] Stammberger finds it surprising that this patch “isn’t available for download on the manufacturer’s website....You’d have to specifically request it, and I don’t know how any enterprise customer would ever find out about the problem unless they attended the Amphion Forum and know what to ask for or who to ask for it.”
About the Author
Charles Q. Choi is a science writer based in New York City. His reporting has appeared in The New York Times, Scientific American, and Wired, among other publications. In September 2011 he reported for IEEE Spectrum on a brain computer interface based on ultrasound.