You would have had to be living on the moon not to know by now that USB flash drives are a serious security risk: They spread computer viruses the way reused needles spread real ones. If you didn’t realize that before, news that the Stuxnet computer worm (which hobbled Iran’s uranium-enrichment program) was distributed through infected flash drives should have clued you in. Now specialists at Security Research Labs in Berlin say that many other types of USB peripherals can also spread malware. They are presenting their ideas next week in Las Vegas at the Black Hat security conference in a talk entitled, “BadUSB—On accessories that turn evil.”
The researcher’s basic thesis is this:
1. Many peripheral devices incorporate special USB-controller chips that themselves can be reprogrammed.
2. There are no protections in place to prevent a malicious party from manipulating one of these USB-controller chips in this way.
3. Such a hack could enable the peripheral to inject malware into your computer, which could do nasty things, including manipulating the firmware in other peripheral devices that you later plug in.
4. Rinse and repeat.
The researchers claim that a USB peripheral could, for example, pretend to be a network card and surreptitiously redirect your Internet communications by changing your DNS settings. Or it could impersonate a keyboard and issue command-line instructions to do almost anything.
What’s not clear, though, is whether these are examples of things that could be done using just the memory available to a typical USB-controller chip. My guess is that these tasks would take more space than what's found in the EEPROMs normally attached to these chips. A keyboard, for instance, might have only an 8 kilobyte EEPROM connected to store such variables as the USB-device description and special key mappings. Malware is typically much bigger. The experimental hacks these researchers have carried out probably run a large chunk of code stored invisibly in the flash memory of a USB thumb drive. If that surmise is correct, it would suggest that USB peripherals with minimal data storage are perhaps not so threatening.
The researchers haven't uncovered an actual instance of this kind of infection in the wild, but they emphasize that there is really no way to protect against such attacks should they come to pass. Malware scanners won’t check the firmware on USB peripherals, so these programs wouldn’t be able to detect an infection, much less remove it. Even a fresh install of your computer’s operating system would be of little use, because it wouldn’t affect what's on peripheral devices. Indeed, it would seem to me that the USB-controller firmware on computers (the “host” side of the USB communications) might also be vulnerable to hacking and would be very difficult to scan or clean.
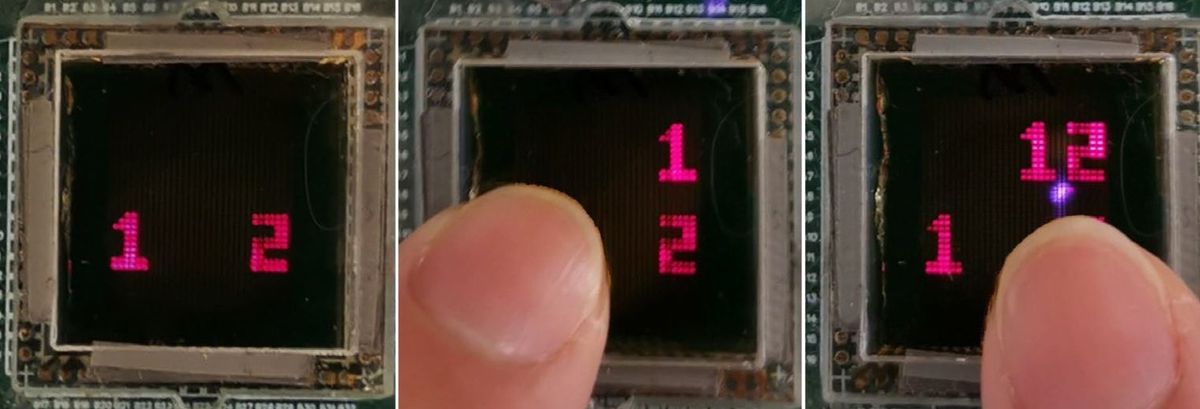
So what’s to be done? In the short term, avoiding USB promiscuity might be a good idea. That’s already de rigueur for thumb drives, which, I'm supposing at the moment, are where the real threat lies here. Over the longer term, though, the manufacturers of USB devices will have to engineer their products so the USB-device firmware simply cannot be modified or so that modification requires some concrete action from the user—a button push or temporary jumper placement. Such a strategy could indeed help prevent malware from spreading to embedded devices of all sorts, including routers and printers, which have also been of concern of late. I for one would welcome the nuisance of a small button push now and again in return for greater piece of mind.
David Schneider is a senior editor at IEEE Spectrum. His beat focuses on computing, and he contributes frequently to Spectrum's Hands On column. He holds a bachelor's degree in geology from Yale, a master's in engineering from UC Berkeley, and a doctorate in geology from Columbia.