What can a 174-year-old French novel possibly have to say about cybersecurity? Quite a lot, it turns out. Alexandre Dumas’s The Count of Monte Cristo was published in 1844, and so he of course knew nothing about the Internet and probably little about electricity. But the writer had a keen understanding of human nature and how people interact with technology, and he saw how technological attacks could by engineered by exploiting personal foibles.
The communications technology at the heart of The Count of Monte Cristo is the telegraph, although not the familiar electric telegraph. That telegraph was still being developed when Dumas was writing his novel. In 1837, Charles Cooke and William Wheatstone demonstrated their electric telegraph system in London, and Samuel Morse patented the idea for his telegraph in the United States.
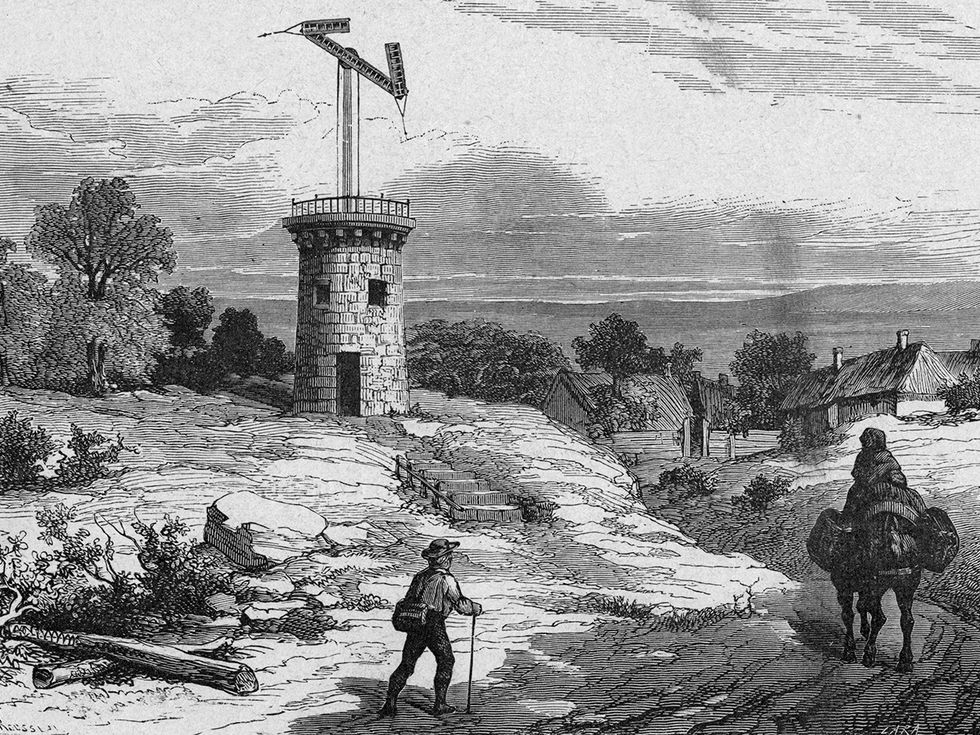
The telegraph of The Count of Monte Cristo is the optical telegraph. Starting in the 1790s, the French built and operated this long-distance communications system, which eventually included two main lines, one running from the English Channel to the Mediterranean and the other from Spain to Belgium. Each line consisted of a string of towers, spaced roughly 10 kilometers apart. At the top of each tower was a semaphore—a large rotatable crossbeam with a short movable arm at each end. When a message was being transmitted, each tower’s operator would adjust the semaphore to match the semaphore at the previous tower; the next tower’s operator would do the same, and so the message would travel down the line. [For a fuller account of how the optical telegraph operated, see Gerald J. Holzmann and Björn Pehrson's The Early History of Data Networks, Wiley 1994.]

The lead engineer on this system was Claude Chappe, who got his idea from semaphore flags, which had been used to send military messages since the time of Alexander the Great. Chappe developed a system of linkages and pulleys to control the semaphore, created a code that both compressed messages and kept them secret, and wrote rules of operation that would, among other things, allow operators to change the direction of communication.
The optical telegraph emerged out of the French Revolution. Chappe started his experiments on the telegraph shortly after the uprising began and the Bastille fell in 1789. After the executions of Louis XVI and Marie Antoinette in 1793, the revolutionary government decided that it needed a national communication network under its own control. At the time, the only long-distance communication was the postal service, which had been organized by Louis XIV and remained heavily influenced by the royal family, the aristocracy, and the clergy—three groups that were enemies of the revolution and hence not to be trusted.
Chappe’s optical telegraph removed the enemies of the revolution from the communications system and replaced them with common citizens, who were paid a modest stipend to operate a semaphore station. Dumas described these operators as “poor wretches” who were under strict discipline, required to stay at their post from dawn to dusk and to spy on their fellow operators, recording every signal that was transmitted incorrectly. “I have no responsibility,” one operator says in The Count of Monte Cristo. “I am a machine then and nothing else.”
The telegraph hack that Dumas came up with is predictable enough. The count, a man who had been unjustly imprisoned in his youth, plants a false message on the telegraph to ruin one of the men who had wronged him. He does this by bribing the operator with enough money to allow him to leave the telegraph service, avoid punishment, and start life afresh elsewhere. The obvious moral here is that people are often the weakest link in a technological system.
But Dumas revealed a second weakness in the system. It was not enough for the count to plant false information. He needed to plant that information in a way that the falsehood would be taken as true. No technology, no matter how novel or powerful, automatically imparts the ring of truth to its messages. The recipients of telegraphic messages would critique and assess any information put into their hands. To emphasize this point, Dumas filled the book with characters who distrust the telegraph. You “think yourself well informed because the telegraph has told you,” one character tells another. “Believe me, we are as well informed as you.”
The count makes his message believable by exploiting a second human weakness in the French communications system. He notes that his victim’s wife is a friend of a government secretary with ready access to the telegraph. The secretary never opens his mouth, but “the stockbrokers immediately stenograph” his words. Yet something in the secretary’s behavior suggests that he has something to hide. Dumas calls it a “mind ill at ease.” The count exploits this uneasy mind. A quiet word from the count gets the secretary to agree to pass the false message to the victim’s wife, who then passes it to her husband. With this agreement, the count’s plan of revenge is complete.
Thus can old technologies teach universal lessons in simple, stark terms. The weakness of the French telegraph was not unique: All communications systems rely on their employees, who must submit to operational rules and organizational discipline and who are susceptible to outside influence. As Dumas’s tale suggests, these systems are also vulnerable to security risks that lie well outside the operational staff.
Readers of The Count of Monte Cristo naturally want to identify with the hero, a man who ultimately gets all that he wants: wealth, knowledge, and revenge on his persecutors. Yet Dumas suggests that we the readers might not be the hero—we might instead be the operator who succumbs to bribery or the secretary who’s willing to undermine the telegraph. Technical weaknesses can be found in all communications systems, but often the greatest weakness is found among the people who operate and use them.
About the Author
David Alan Grier is a computer scientist and writer. He is the author of When Computers Were Human (Princeton, 2005) and is the CTO and a co-principal of the consulting firm Djaghe LLC.



