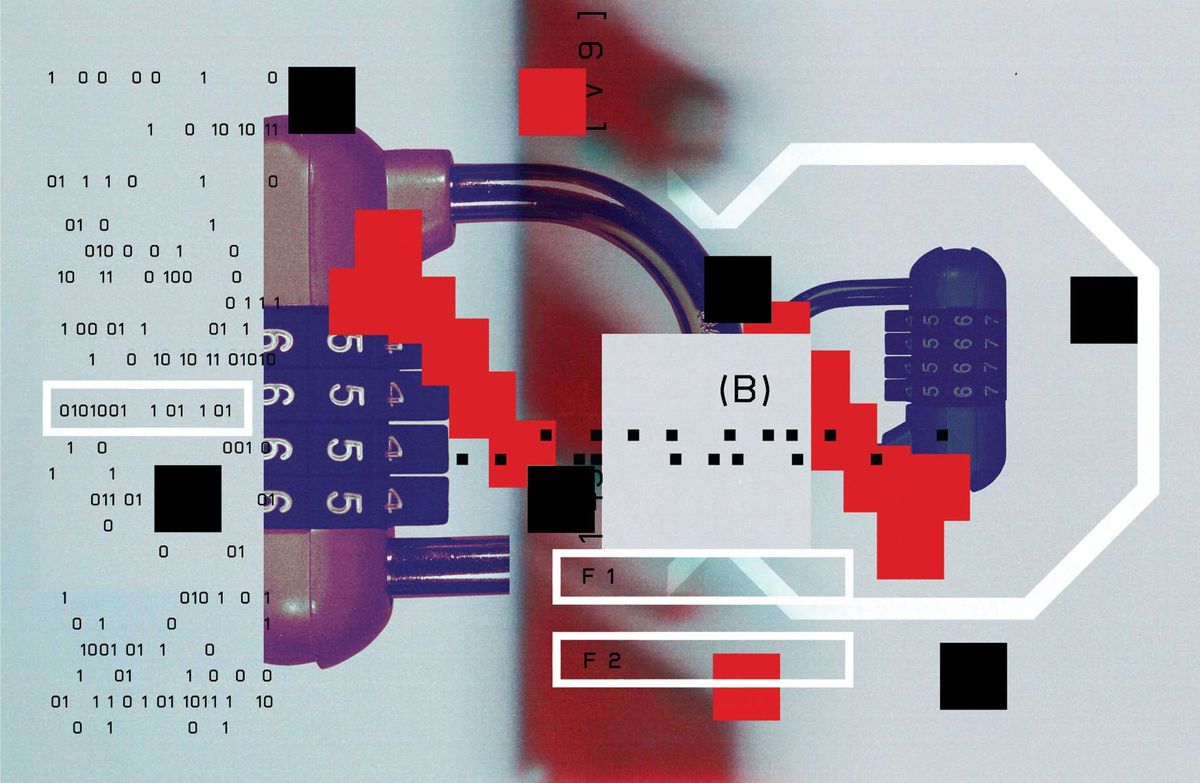
Anonymous sources face a huge challenge in leaking sensitive information to journalists without leaving a digital trail for government investigators to follow. The New Yorker aims to make anonymous leaks feel slightly more secure with its new "Strongbox" solution, but the system's security still ultimately depends upon the caution of its users.
The New Yorker's drop box allows sources to upload documents anonymously and provides two-way communication between sources and journalists, according to The Guardian.
Sources are able to upload documents anonymously through the Tor network onto servers that will be kept separate from the New Yorker's main computer system. Leakers are then given a unique code name that allows New Yorker reporters or editors to contact them through messages left on Strongbox.
Strongbox is based on an open-source, anonymous in-box system called DeadDrop—the brainchild of security journalist Kevin Poulsen and Internet pioneer and activist Aaron Swartz from almost two years ago. Poulsen described how Swartz had created a stable-enough version of the DeadDrop code by December 2012 for them to set a tentative launch date. On 11 January 2013, Swartz killed himself as he faced the possibility of a a 35-year prison sentence for downloading 4 million articles from the JSTOR academic database.
The Strongbox launch on 15 May comes at a time when the U.S. government has shown itself willing to go after information leakers—and possibly reporters—by any means necessary. The Associated Press has reported on how the Justice Department secretly obtained phone logs used by AP editors and reporters. In another case, a Fox News chief correspondent may face criminal charges for reporting on a classified CIA analysis of North Korea provided by a source in the State Department.
Such relentless pursuit of information leaks presents both sources and journalists with several huge challenges. Sources want an easy, secure way to share information anonymously with news organizations. Journalists want the same thing, but also have the additional worries of needing to verify the information and get in contact with the source.
Thus far, online tools represent an easy but insecure way for anonymous sources to share sensitive information with journalists. Solutions such as Strongbox can help make anonymous leaks more secure, but security comes at the price of making the sharing process more cumbersome—a possible deterrent for would-be sources. For instance, Strongbox's use of the Tor network helps protect the identities of people uploading files. But the Tor system can prove tricky for novice computer users to install and navigate, according to several experts quoted by Knight-Mozilla's Source news.
The balance between security and ease-of-use also emerges in Strongbox's communication scheme. Security would depend upon "perfect operational discipline" by both the anonymous source and journalists, says Jacob Harris, a senior software architect at the New York Times, in an email published by Knight-Mozilla's Source news.
"A perfect communication system would be slow and onerous to use, and both sides might be tempted to bypass it and talk via other channels. In short, people are generally the source of security lapses, and we can’t forget that here."
Digital drop boxes have faced uncertainty since the height of Wikileaks' success in 2010, The Guardian points out. The Wall Street Journal's SafeHouse drop box that launched in 2011 faced criticism for glitches that could compromise the anonymity of sources. The New York Times considered a similar online tool in 2011 but did not proceed with the plan. And Al Jazeera's drop box has yet to lead to any huge leaks. Maybe that's because, at the end of the day, no system is foolproof. That's probably the rationale behind the final line in the New Yorker's privacy promise regarding Strongbox: "The system is provided on an 'as is' basis, with no warranties or representations, and any use of it is at the user's own risk."
So the challenge of ensuring security for anonymous leakers remains. But the New York Times's Harris suggested that news organizations may want to put just as much focus on making it easier for sources not as concerned about anonymity to pass along information. He pointed to Bradley Manning, a U.S. Army intelligence analyst facing possible life in military prison for leaking classified U.S. documents to WikiLeaks. In that case, Manning had previously failed to find a way to hand over his digital documents to the Washington Post, New York Times, and Politico.
Photo: okeyphotos/iStockphotos
Jeremy Hsu has been working as a science and technology journalist in New York City since 2008. He has written on subjects as diverse as supercomputing and wearable electronics for IEEE Spectrum. When he’s not trying to wrap his head around the latest quantum computing news for Spectrum, he also contributes to a variety of publications such as Scientific American, Discover, Popular Science, and others. He is a graduate of New York University’s Science, Health & Environmental Reporting Program.