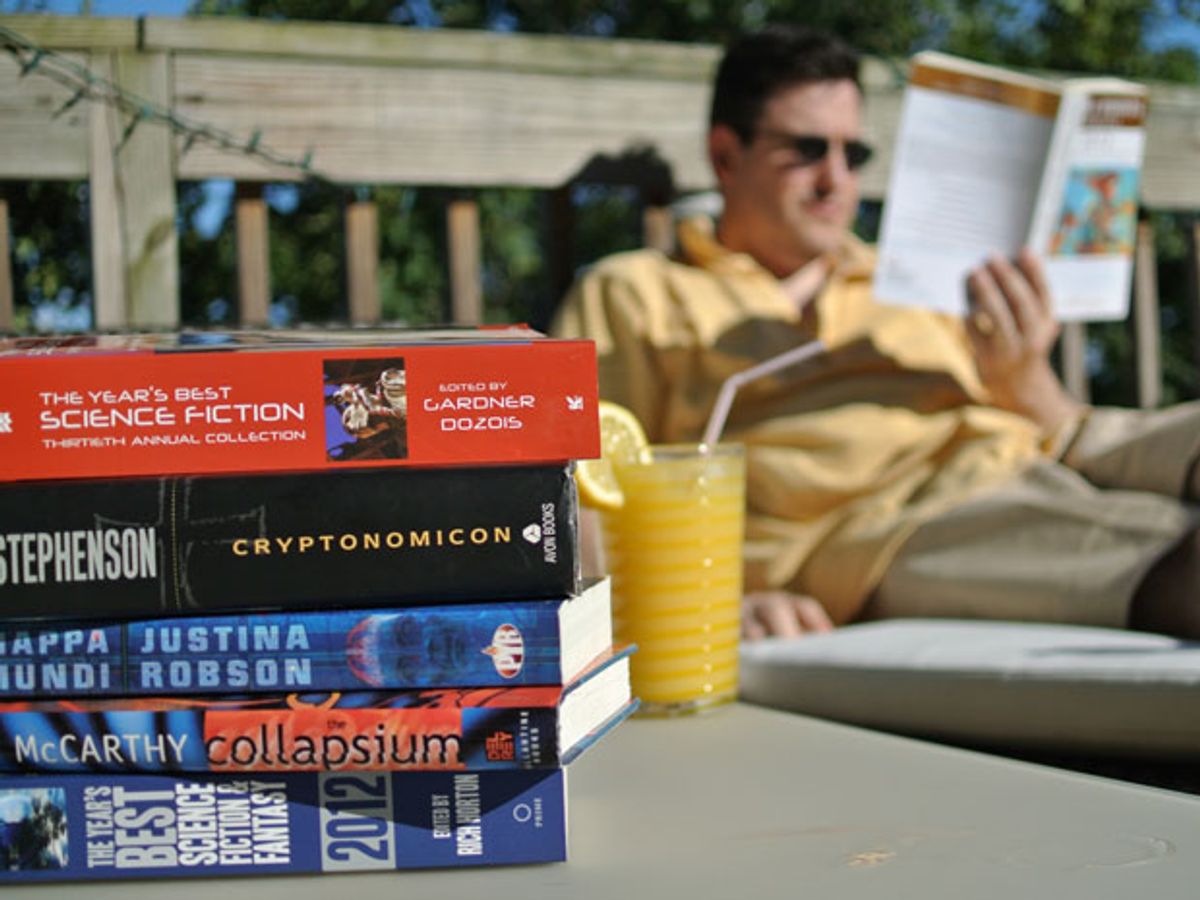
Summer vacations are a great time to lean back and relax with a good book (or e-book). For the technically inclined who enjoy science fiction and don’t mind a busman’s holiday, here are some suggestions—stories, novels, and multivolume series involving some mix of electronics, engineers, computers, networks, programming, robots, AI, and maybe even a few vacuum tubes.
I’ve limited recommendations to things readily available in paper or digital versions. In general, I’ve given the Amazon link that includes the Kindle version, but assuming you can’t find a copy in your bookshelf or local library, there are lots of other brick-and-mortar and online booksellers, new and used, out there.
If an engineering theme doesn’t appeal to you, and you’re just looking for SF recommendations in general, it’s always a good idea to start with the winners and nominees of the Hugo Awards, selected annually by science fiction fans, and of the Nebula Awards, selected annually by members of the Science Fiction Writers of America. There are also the Locus Awards, selected by readers of Locus, the leading magazine/site covering the science fiction and fantasy field, not to mention the various best “SF of the year” anthologies like the Year’s Best SF series, edited by David Hartwell and Kathryn Cramer; The Year’s Best Science Fiction series, edited by Gardner Dozois; and The Year’s Best Science Fiction & Fantasy series, edited by Rich Horton.
A few classics you should read, if you haven’t already, or may enjoy rereading:
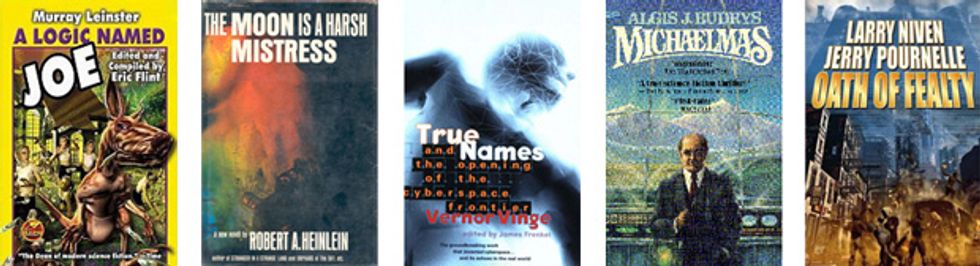
“A Logic Named Joe,” by Murray Leinster (March 1946, in Astounding Science Fiction magazine, but available online for free). Leinster’s story anticipated the Web—and the potential dangers of unrestricted information.
The Moon Is A Harsh Mistress, by Robert A. Heinlein (1966) and Michaelmas, by Algis J. Budrys (1977). Two classic novels about self-aware computers.
True Names, by Vernor Vinge (1981) One of my top 10 science fiction/fantasy favorites, True Names is a compelling tale of gamers, cyberspace, bots, avatars, and more. Originally published as a thinnish trade paperback, it’s now the opening item in the fact-and-fiction collection True Names: And the Opening of the Cyberspace Frontier (2001).
Oath of Fealty, by Larry Niven and Jerry Pournelle (1981). Might you prefer to live in a city-size building with ubiquitous security surveillance, a central computer, and senior execs with computer-link brain implants?
And more recent goodies:
How would you compute or communicate when it’s not safe to use any electricity? You might do it via “meatware”—picture thousands of people acting like computational components and signaling via mirrors. Read the Greatwinter Trilogy by Sean McMullen: Souls in the Great Machine (1999), The Miocene Arrow (2000), and Eyes of the Calculor (2001).
If you like your science fiction technodense and cynically humorous, settle down with former code monkey Charles Stross. A good place to start is The Atrocity Archives (2004), one of Stross’s Laundry Files series of novels), where computer desk jockeys get mashed into Leonard Deighton/H.P. Lovecraft scenarios. Or if you’re up for a physics-intensive interstellar romp with post-singularity AIs, faster-than-light causality, cornucopia replicators, and more, try Stross’s Singularity Sky (2003).
Cryptography’s the thing, in Cryptonomicom, by Neal Stephenson (1999). This sprawling book includes the Solitaire encryption algorithm, created by Bruce Schneier for the novel, which permits you to encode a message using a deck of playing cards (the full details of which are explained in an appendix).
When Sysadmins Ruled the Earth, by Cory Doctorow (2006).
What if the World Wide Web became sentient? Robert J. Sawyer came up with an intriguing way how, and what might happen, in his WWW trilogy: Wake (2009), Watch (2010), and Wonder (2011).
That’s only scratching the surface, of course. There are great reads by Wil McCarthy, William Gibson, Rudy Rucker, Bruce Sterling, hundreds of short stories and novelettes in magazines and collected in theme and “Best of” anthologies. (Recognizing that I was having trouble thinking of women authors writing in this space, I asked veteran science fiction book reviewer and author Don D’Ammassa, who suggests: Synners, by Pat Cadigan (1991), Dreamships, by Melissa Scott (1992), and Silver Screen,by Justina Robson (1999). [Also, Robson’s Mappa Mundi—ed.])
Did we miss any must-reads? Let us know in the comments below. But this should be more than enough to get you through the rest of summer and into mid-fall, although, of course, winter is coming...
About the Author
Daniel P. Dern is a Boston-based freelance technology and business writer. He also writes stories with science fiction, Jewish, and kids’ themes—and has read and reread more than his share of science fiction books over the decades.
Daniel P. Dern is a freelance journalist. He writes about the careers of engineers as well as a variety of technology topics.