A top military official says there’s a simmering shadow conflict playing out in space, with U.S. satellites coming under regular attack. But what does an attack on a spacecraft look like, who is committing them, and how can operators protect themselves?
General David Thompson, the vice chief of space operations at the US Space Force, recently told the Washington Post that China and Russia are targeting U.S. government satellites on a daily basis. While that might conjure up images of satellites being blown out of orbit left, right, and center, the reality is more low-key.
Thompson said the bulk of the incidents they’re seeing are “reversible attacks”, which temporarily disrupt a satellites operations rather than causing permanent damage. This can be achieved in a variety of ways, from jamming satellite signals to carrying out cyber-attacks.
“I would call those activities concerning, because there isn't a shared understanding of where the thresholds are for retaliation.”
—Laura Grego, MIT
These kinds of attacks exist in a legal and political gray area, says Laura Grego, a Stanton Nuclear Security Fellow at the MIT Laboratory for Nuclear Security and Policy. But while most states don’t currently treat them as acts of war, the lack of clarity and their growing frequency is a worry.
“They’re testing the boundaries, trying to explore how far you can go before you get a reaction,” says Grego. “I would call those activities concerning, because there isn't a shared understanding of where the thresholds are for retaliation.”
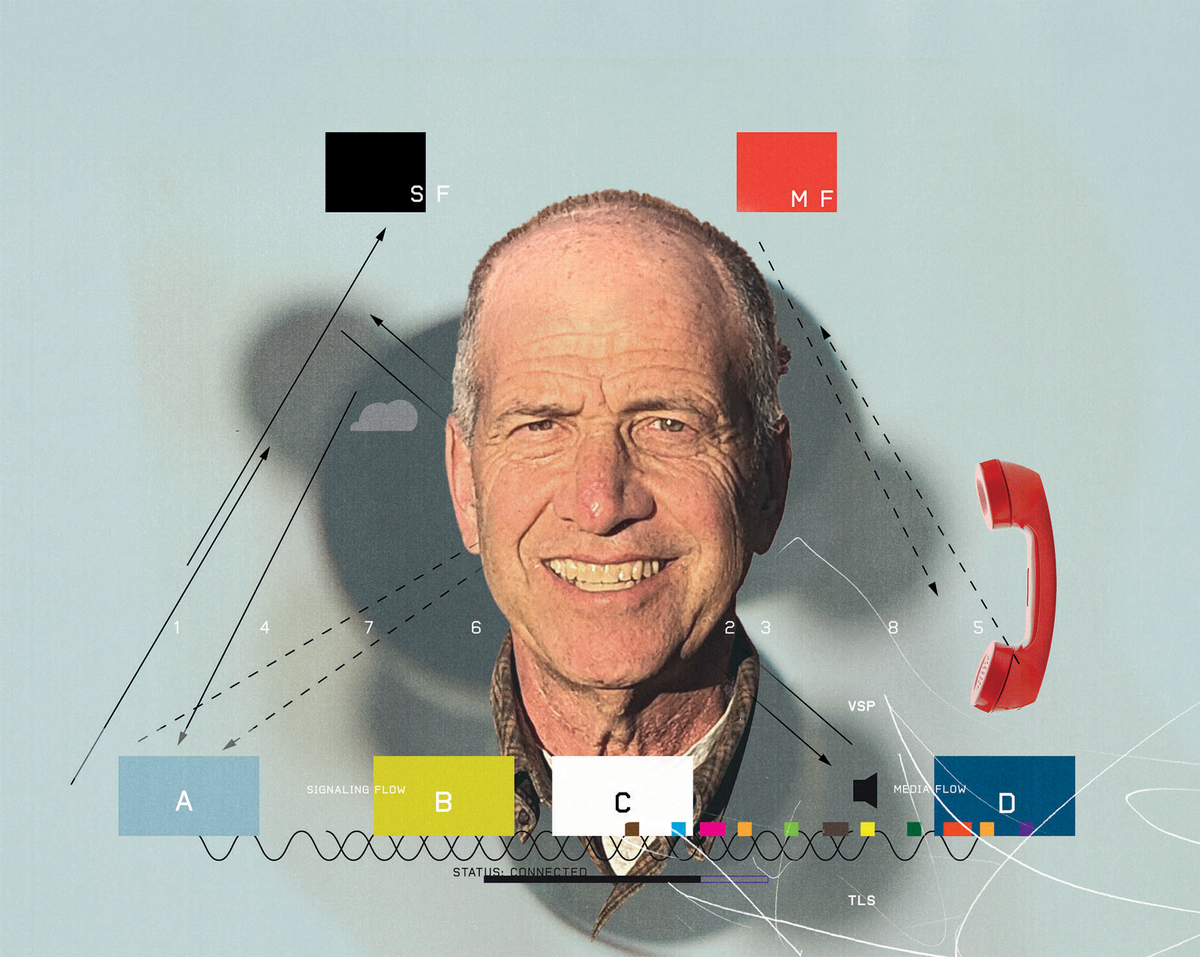
The most common kind of attack involves interfering with the radio signals coming to and from satellites, particularly those used by GPS satellites, Brian Weeden, director of program planning at the Secure World Foundation, writes in an email. This can involve beaming a signal from a ground-based transmitter at a satellite to interfere with its ability to pick up communications from its control station. Alternatively, it’s possible to direct a rogue transmission towards ground receivers to block the signal, or replace it with a fake one, something known as spoofing.
A 2019 report from security research non-profit C4ADS found evidence that Russia regularly uses jamming and spoofing attacks against GPS satellites to protect sensitive locations from drone attacks or surveillance. But the US also has similar capabilities - last year the US Navy tested GPS jamming technology that interfered with signals across six states.
The US, Russia and China have also all developed ground-based laser systems designed to dazzle the optical sensors of spy satellites as they pass over sensitive sites. “That's akin to shining a really bright flashlight in someone's eyes,” writes Weeden. “It can temporarily prevent the satellite from taking a picture, or in some cases might actually physically damage the [image sensor] if it's strong enough. ”
The advent of software-defined radios has made it far easier and cheaper to carry out jamming and spoofing attacks on satellites.
The leading space powers still have the capability to commit more obvious acts of war in space. Russia recently drew widespread condemnation for testing an anti-satellite missile on one of its own defunct surveillance satellites, and the US, China, and India have all carried out similar tests. One disincentive to carrying out this kind of attack, however, is that it litters Earth’s orbit with debris that can unintentionally damage other spacecraft, says Grego.
There are ways to physically attack a satellite without causing so much collateral damage, though. So-called “co-orbital anti-satellite weapons” are essentially spacecraft that can maneuver close to an adversary's satellite before attacking them with a projectile or clawing at them with a robotic arm to cause damage. They can also be used to snoop on enemy satellites, says Grego, either to intercept signals or try to work out what their mission is.
In 2020, a pair of Russian spacecraft were spotted tailing a US spy satellite and a few months later one of them was seen releasing a fast moving projectile. So far though, there have been no reports of anyone carrying out a physical attack on another country’s satellite, says Grego.
Attacks on spacecraft are no longer just the preserve of nation states though, says Frank Schubert, from Airbus Cybersecurity. The advent of software defined radios, which use a digital processor rather than specialized electronics to modulate radio signals, has made it far easier and cheaper to carry out jamming and spoofing attacks. And in 2019, researchers showed that they could intercept signals from a satellite broadband service and identify users and their browsing activity using just €285 ($322) worth of equipment.
Satellite operators are also subject to constant attacks from hackers, says Schubert. Typically, these are targeted at the ground stations that control and communicate with satellites, but if successful could be used to do everything from steal data to interfere with the operation of spacecraft. There’s also a growing threat from “hybrid attacks”, says Schubert. For instance, attackers might jam a signal from a satellite and quickly follow this up with a well-crafted phishing email to the operator claiming to be able to resolve the problem.
Countering these threats involves following the same kinds of cybersecurity best practices as any other industry. But given the complex supply chains involved in building spacecraft it’s also critical to ensure the provenance of every part of the system. “Security by design is key,” says Schubert. “I can have the best defense for cyber-attacks, but if the bug is already inside my system that went in through the supply chain, I'm in big trouble.”
Another important way to counteract many of these threats is to build resiliency into space systems, says Grego. This could involve investing in the ability to rapidly launch replacement satellites or swapping a single large, expensive satellite with a network of smaller ones that can still operate if one or two are knocked out.
Edd Gent is a freelance science and technology writer based in Bengaluru, India. His writing focuses on emerging technologies across computing, engineering, energy and bioscience. He's on Twitter at @EddytheGent and email at edd dot gent at outlook dot com. His PGP fingerprint is ABB8 6BB3 3E69 C4A7 EC91 611B 5C12 193D 5DFC C01B. His public key is here. DM for Signal info.