News reports surfaced last night and this morning that SecurID, the major two-factor authentication security product of RSA (which is the security division of the EMC Corporation), has been the target of a sophisticated cyber attack.
As described by the Boston Globe this morning:
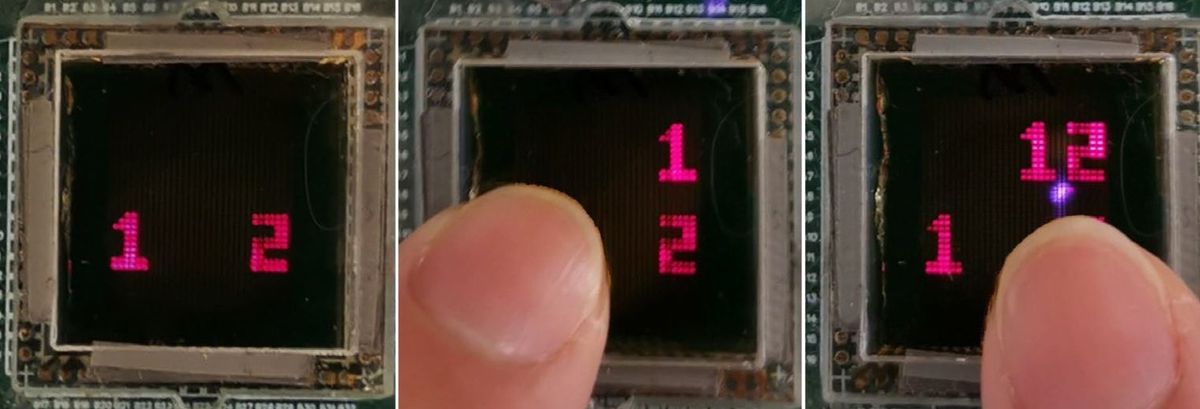
"SecurID is used by 40 million people in 30,000 organizations worldwide, including banks and government agencies... SecurID randomly generates a number once a minute, displaying it on a small device carried by a user. To gain entry to a computer network protected by SecurID, the user must type in this number, along with a traditional password."
EMC outlined the attack in an 8-K filing with the US Security and Exchange Commission (SEC) late yesterday. In the filing, EMC wrote that:
"Recently EMC’s security systems identified an extremely sophisticated cyber attack in progress, targeting our RSA business unit. We took a variety of aggressive measures against the threat to protect our business and our customers, including further hardening of our IT infrastructure. We also immediately began an extensive investigation of the attack and are working closely with the appropriate authorities."
"Our investigation has revealed that the attack resulted in certain information being extracted from RSA’s systems. Some of that information is related to RSA’s SecurID two-factor authentication products. While at this time we are confident that the information extracted does not enable a successful direct attack on any of our RSA SecurID customers, this information could potentially be used to reduce the effectiveness of a current two-factor authentication implementation as part of a broader attack."
Arthur Coviello, Jr., Executive Chairman of RSA further elaborated on the situation in an open letter to RSA customers:
"Our investigation has led us to believe that the attack is in the category of an Advanced Persistent Threat (APT)... We have no evidence that customer security related to other RSA products has been similarly impacted. We are also confident that no other EMC products were impacted by this attack. It is important to note that we do not believe that either customer or employee personally identifiable information was compromised as a result of this incident... We regret any inconvenience or concern that this attack on RSA may cause for customers."
RSA has issued nine recommendations to its customers to deal with the risk posed by the hacking attempt. These are aimed at tightening up organizational security practices, watching for signs of a possible security breach such as unusual changes in user privileges and access rights, and "harden[ing], closely monitor, and limit remote and physical access to infrastructure that is hosting critical security software."
EMC, in its SEC filing, said that based on what it knows now:
"EMC does not believe that the matter described in the letter and note will have a material impact on its financial results."
If a successful hack of SecurID is reported, expect that to change considerably.
Robert N. Charette is a Contributing Editor to IEEE Spectrum and an acknowledged international authority on information technology and systems risk management. A self-described “risk ecologist,” he is interested in the intersections of business, political, technological, and societal risks. Charette is an award-winning author of multiple books and numerous articles on the subjects of risk management, project and program management, innovation, and entrepreneurship. A Life Senior Member of the IEEE, Charette was a recipient of the IEEE Computer Society’s Golden Core Award in 2008.