The famous Stuxnet computer virus that sabotaged Iran’s nuclear program apparently had a cousin designed to do the same to North Korea. But this other U.S. cyber attack failed because agents could not physically access the isolated computers of North Korea’s nuclear program.
Several U.S. intelligence sources told Reuters that the operation aimed at North Korea took place at the same time as the Stuxnet attack that crippled Iran’s nuclear program in 2009 and 2010. The Stuxnet virus worked by hijacking the control software of fast-spinning centrifuges belonging to Iran’s nuclear program. Once activated, Stuxnet caused physical destruction by forcing the centrifuges to spin out of control and tear themselves apart. The U.S. National Security Agency led a similar, unsuccessful effort with a modified Stuxnet aimed at taking down North Korean centrifuges.
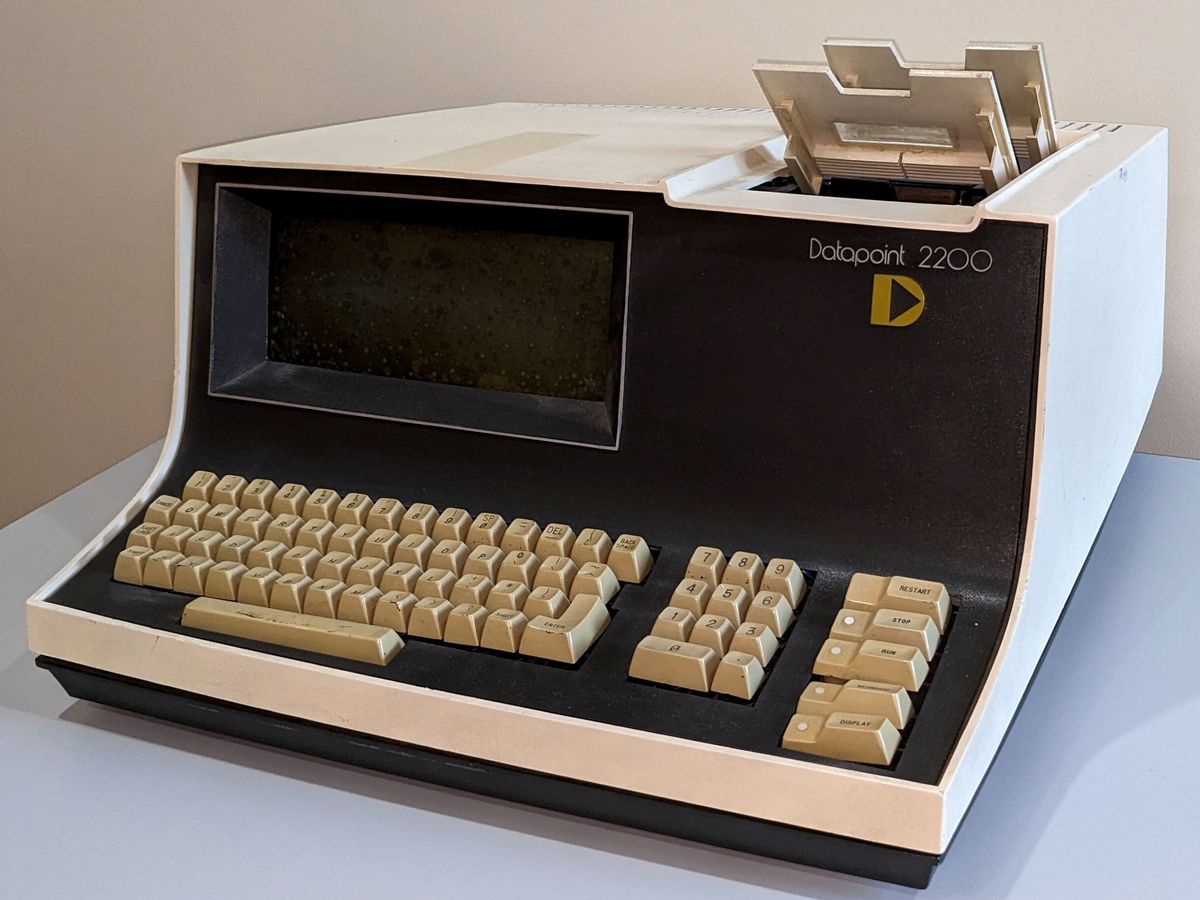
Both Iran and North Korea likely use similar centrifuges that can enrich uranium for either civilian purposes or to become weapons-grade nuclear material. That means North Korea probably also uses control software developed by Siemens AG running on some version of Microsoft Windows, experts told Reuters.
Stuxnet, a joint effort between the United States and Israel, worked in three phases to infiltrate and attack its targets. First, it continually infected Microsoft Windows machines and networks while replicating itself. Second, it looked for Siemens Step7 software that forms the foundation of industrial control systems for operating equipment such as centrifuges. Third, it hijacked the programmable logic controllers so that it could provide secret surveillance on the centrifuges or command the centrifuges to act in a self-destructive manner.
The computers running the control systems for centrifuges belonging to the nuclear programs of Iran and North Korea are isolated from the Internet to avoid providing easy access for cyber attacks. That’s why Stuxnet relied on first spreading stealthily across many Internet-connected machines, in hopes of a worker sticking a USB thumb drive into an infected machine. Stuxnet could then infect the USB drive and eventually make its way to computers isolated from the Internet. (See IEEE Spectrum’s feature “The Real Story of Stuxnet.”)
But North Korea presented an even greater challenge than Iran because of its extreme isolation. Relatively few North Koreans have access to the open Internet, and computer ownership requires registration with the police. In any case, the United States failed to get its Stuxnet-style virus onto the machines controlling North Korea’s centrifuges.
Many experts interviewed by Reuters doubted that a Stuxnet-style virus would have made much impact on North Korea’s nuclear program even if it had succeeded. That’s in part because North Korea likely has at least one other hidden nuclear facility beyond the known Yongbyon nuclear complex. But it’s also because North Korea likely has access to plutonium, which does not depend on the complex uranium enrichment process.
Jeremy Hsu has been working as a science and technology journalist in New York City since 2008. He has written on subjects as diverse as supercomputing and wearable electronics for IEEE Spectrum. When he’s not trying to wrap his head around the latest quantum computing news for Spectrum, he also contributes to a variety of publications such as Scientific American, Discover, Popular Science, and others. He is a graduate of New York University’s Science, Health & Environmental Reporting Program.