One of ISIS’ most dangerous weapons has been the Internet. The extremist group relies heavily on social media to spread news and recruit soldiers. And many “lone wolf” criminals including the couple that terrorized San Bernardino, Calif. and the Orlando shooter, are thought to have been radicalized at least in part online.
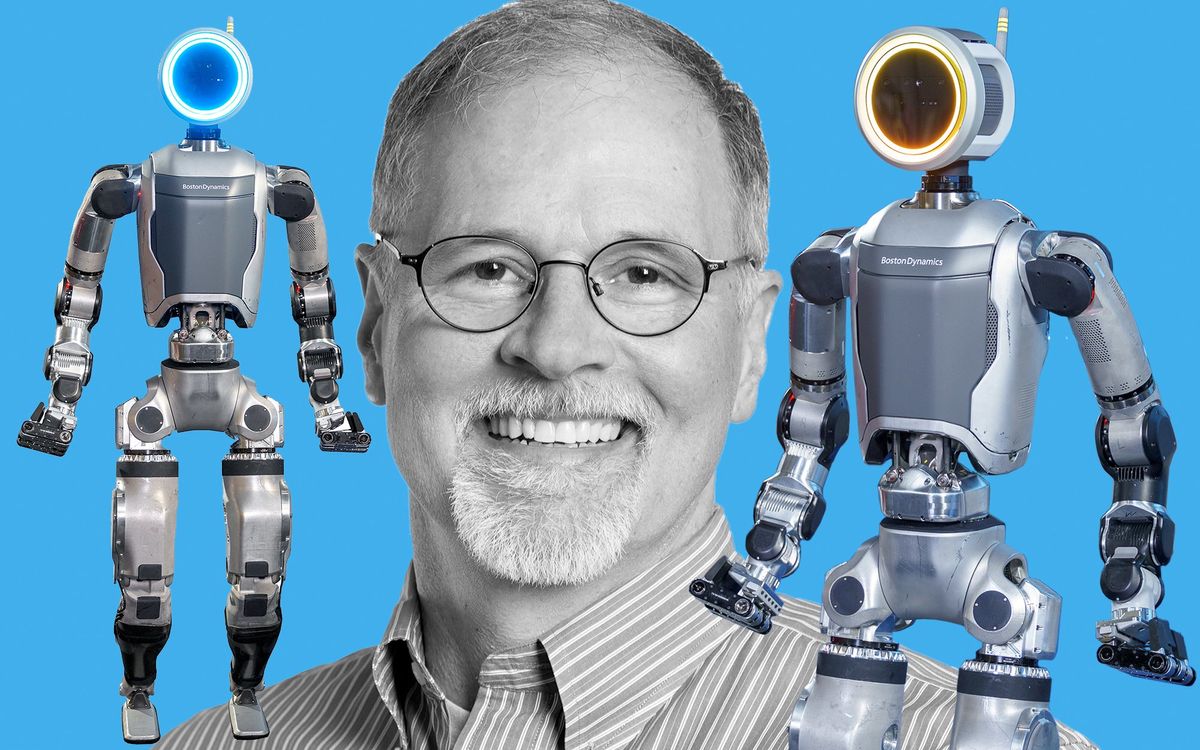
Counterterrorism units and law enforcement agencies have struggled to fight back against these new virtual tactics. Now, computer scientists led by Stefan Wuchty at University of Miami have released the first formal survey of how pro-ISIS online groups behave. In particular, their work identifies three popular strategies many groups have used to evade censorship in social media networks. They published their work in Science on Thursday.
“Social media has been a very valuable tool for ISIS,” says J.M. Berger, a fellow with George Washington University’s Program on Extremism. “ISIS is the first extremist group to really operationalize it, but it certainly won't be the last.”
Back at the University of Miami, Wuchty’s team analyzed pro-ISIS groups on the social networking site VKontakte, which has more than 350 million users primarily from Russia and Europe. The group monitored VKontakte because it often allows groups to remain online longer, whereas Facebook and Twitter quickly shut down pages related to terrorism.
Every day for the first eight months of 2015, software designed by Wuchty’s team combed VKontakte for pro-ISIS online groups. Subject matter experts (two graduate students from the international studies program) identified hashtags for algorithms to search and manually reviewed the results to verify that the selected groups were pro-ISIS.
In the end, the team logged 196 pro-ISIS groups with 108,086 followers on VKontakte during the study period. Followers used these groups to find the latest ISIS news, swap survival tips, and contribute to fundraising campaigns for soldiers traveling to Syria.
“This is the largest study I've seen which is data-driven looking at how ISIS supporters group together on any social network,” says V.S. Subrahmanian, a computer scientist who focuses on culture and policy studies at the University of Maryland.
Since the team had tracked these groups daily, researchers could observe the tactics that pro-ISIS groups use to evade authorities. They found that 15 percent of groups changed their names during the study period, and 7 percent flipped their visibility from public to members only. Another 4 percent underwent what the researchers called reincarnation. That means the group disappeared completely but popped up later under a new name and earned more than 60 percent of its original followers back.
The researchers compared these behaviors in the pro-ISIS groups to the behaviors of other social groups made up of protestors or social activists (the entire project began in 2013 with a focus on predicting periods of social unrest). The pro-ISIS groups employed more of these strategies, presumably because the groups were under more pressure to evolve as authorities sought to shut them down.

For now, most of the pro-ISIS groups remain disjointed and loosely coordinated. However, Wuchty’s model suggests if these groups were to grow freely, they could form a mega-network through which ISIS information would very quickly spread. He says this means it’s particularly important for authorities to quash groups soon after they form.
“What our results essentially suggest is, forget about the individuals,” Wuchty says. “Concentrate on the groups because those people who perpetuate such crimes are members of the groups. If you go after the small ones, large aggregates would not emerge.” His research did not specify what size is too big.
Subrahmanian at University of Maryland says law enforcement would need to apply that strategy to as many social media sites as possible because ISIS followers easily jump from platform to platform.
“I think the paper did an outstanding job looking at VKontakte, however, I think the jury is still out on how this would apply to the fact that ISIS is a very versatile organization,” Subrahmanian says. “They understand social media pretty well and they are not likely to be bound by the constraints of operating on just one social media platform.“ Wuchty is willing to share the list of pro-ISIS groups that he has compiled with VKontakte if the company requests it, though says it’s probably outdated by now.
Wuchty and his co-authors also hinted at the idea that monitoring the behavior of pro-ISIS online groups might someday be used to indicate favorable conditions for an attack. Their hypothesis is that new online groups form at a faster rate right before an attack.
The team developed algorithms based on this theory that retroactively identified a blip in activity during the 2014 ISIS assault on the Syrian city of Kobane. However, Subrahmanian says they would need to test the algorithms in real time on a new data set that wasn’t used to develop the original algorithms in order to verify it. Wuchty would like to continue to develop the prediction capabilities of his model, a task that would probably require about $2 million over the next three years.
Berger, the extremism expert, agrees. “I think some of their conclusions may be too ambitious, like the fact that they can broadcast an attack on the basis of a single data point,” he says. The good news, he adds, is the amount of ISIS-related online activity has dropped over the past two years.