According to Google, North Korean-backed hackers are pretending to be security researchers, complete with a fake research blog and bogus Twitter profiles. These actions are supposedly part of spying efforts against actual security experts.
In an online report posted on 25 January, Google's Threat Analysis Group, which focuses on government-backed attacks, provided an update on this ongoing campaign, which Google identified over the past several months. The North Korean hackers are apparently focusing on computer scientists at different companies and organizations working on research and development into computer security vulnerabilities.
“Sophisticated security researchers and professionals often have important information of value to attackers, and they often have special access privileges to sensitive systems. It is no wonder they are targets,” says Salvatore Stolfo, a computer scientist specializing in computer security at Columbia University, who did not take part in this research. “Successfully penetrating the security these people employ would provide access to very valuable secrets.”
North Korea has previously been linked with a number of cyber-attacks, including the 2014 hack of Sony. “They are a nation-state actor with considerable resources. They are not inconsequential,” Stolfo says. For instance, “They executed a large-scale campaign to steal $2 billion to fund their weapons development,” he notes.
There are three reasons Stolfo can think of to explain why North Korea would target these researchers: gathering intel from targets with special access or secrets; “bragging rights to show how powerful they are, that they can pierce the security of even the most sophisticated security researchers and professionals; and retaliation for causing fails of their previous attack attempts. Could very well be a combination of all three.”
In the new study, Google notes the hackers' sham blog contained analyses of publicly disclosed security vulnerabilities, as well as “‘guest’ posts from unwitting legitimate security researchers—likely in an attempt to build additional credibility with other security researchers,” Adam Weidemann, a researcher with Google's Threat Analysis Group, says in the report.
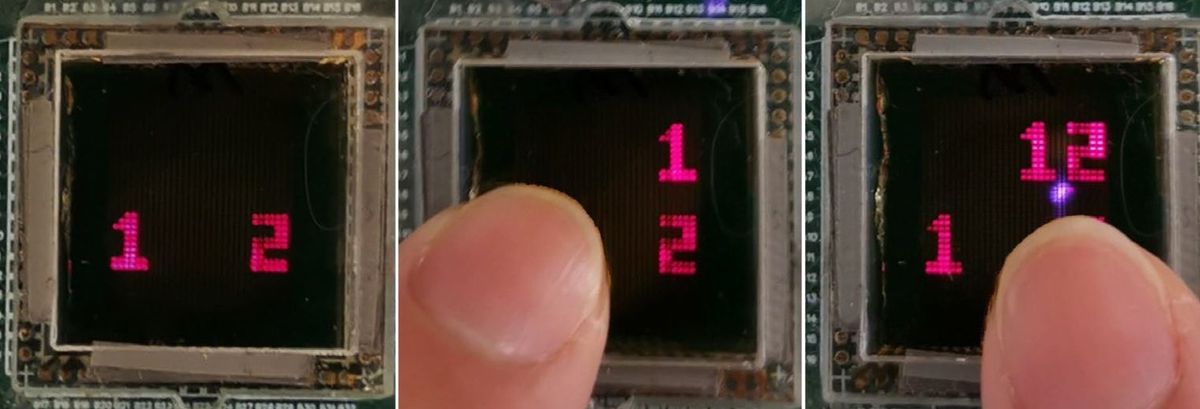
Using multiple Twitter profiles, the hackers posted links to their blog, as well as videos of their claimed exploits of security vulnerabilities. Although Google wasn't able to verify the authenticity or working status of all the exploits for which they posted videos, in at least one video, the hackers faked the success of an exploit. When multiple comments on YouTube identified that video was faked, the hackers then used one of their Twitter profiles to insist it wasn't fake.

“Deception requires believability in the decoys presented to potential victims,” Stolfo says. “In this case, they established a believable social media presence to gain the trust of security researchers. It was an initial important element in their overall strategy to lure their victims.”
Google noted several cases where visiting the blog via a link on Twitter apparently led to malware infecting the victims’ computers. Google noted that it was unable to confirm exactly how the hacked systems were compromised, as at the time of these visits, the victim systems were running fully patched and up-to-date versions of Windows 10 and the Chrome browser.
“We welcome any information others might have,” Weidemann says in the report. “Chrome vulnerabilities, including those being exploited in the wild, are eligible for reward payout under Chrome's Vulnerability Reward Program. We encourage anyone who discovers a Chrome vulnerability to report that activity via the Chrome VRP submission process.”
In addition, once the hackers started talking with their potential victims, they would ask their targets if they wanted to collaborate on research via a Microsoft Visual Studio Project. Those projects would be doped with malware.

“Sharing of code is easy,” Stolfo says. “Here, the attackers were happy to share malcode, which is also easy.”
The hackers used multiple platforms to communicate with potential targets, including Twitter, LinkedIn, Telegram, Discord, Keybase and email. Google provided a list of their known accounts and aliases in the report.
“To date, we have only seen these actors targeting Windows systems as a part of this campaign,” Weidemann adds in the report.
Stolfo notes that ordinary computer users “aren't likely to be targeted by sophisticated nation-state actors except via influence campaigns to shape their opinions. The biggest threat to ordinary users is falling prey to phishing campaigns to steal their digital identities, as well as attacks on their machines to incorporate them into botnets, or to be marshaled for bitcoin mining.”
In general, Stolfo notes that security professionals seeking to defend against such threats should remember basic safeguards: In addition to keeping all their software up to date with the latest security patches once they are released, they should use strong password and multi-factor authentication for any network services that are accessed. What’s more, he says, they should employ the best technologies to secure communications, such as utilizing a virtual private network (VPN) when connecting to an important network. “Most professionals will do these security hygiene functions as second nature,” Stolfo says.
All in all, “One would think it is harder to trick seasoned professional researchers in security who have a natural tendency to trust no one and no thing, but they are all humans first,” Stolfo says. “The human in the loop is hard to secure; even those who design the loop.”
Charles Q. Choi is a science reporter who contributes regularly to IEEE Spectrum. He has written for Scientific American, The New York Times, Wired, and Science, among others.