One of the perks of having an electric vehicle is that its massive batteries allow it to do stuff for you even while the engine is off. Like, you can turn on the heat or the air conditioning in advance to make the car habitable before you need to use it. Unfortunately, if you’ve owned a Nissan Leaf for more than a week, anyone else could potentially have turned your heat or A/C on and off as well, thanks to a gaping security hole that turned a VIN number into an all-access pass to a vehicle’s climate control and historical trip info.
Nissan Leaf owners get access to an app called NissanConnect. Once you set it up and get it talking to your car, it’ll let you remotely activate the climate control system, as well as provide you with a history of trips you’ve taken in the vehicle.
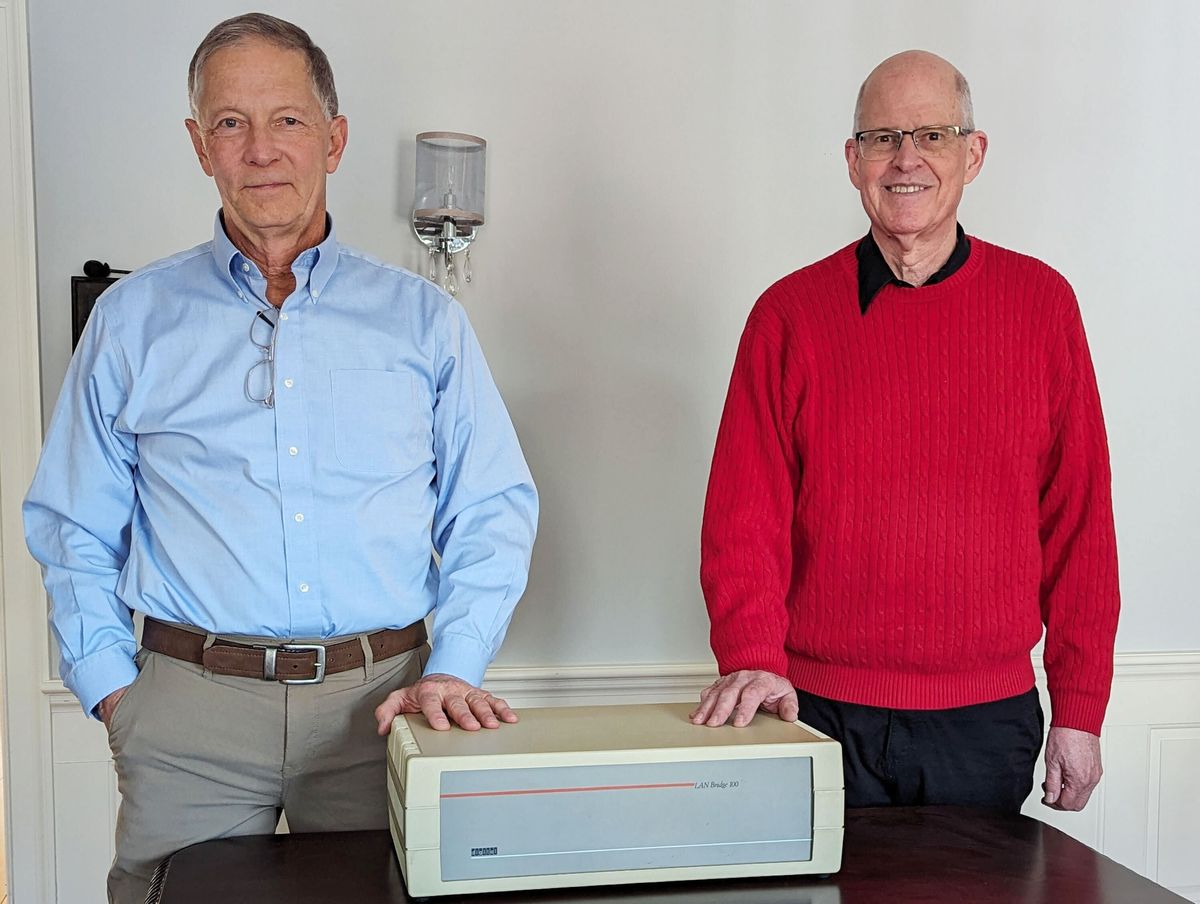
Security researchers Troy Hunt and Scott Helme, acting on a tip from an online forum, confirmed that when a Leaf interfaces with the NissanConnect app through one of Nissan’s servers, information is provided about the state of any vehicle that you have a VIN number for. Essentially, the API allows you to ask, “what is the status of the battery of the Nissan Leaf with VIN number X,” and it’ll return an answer, without any verification, they wrote in a blog post. You can get battery and charging information, climate control status, and even details about past trips that the car has taken. These data don't include locations, fortunately, but they do include dates, times, distances, and even a measure of driving efficiency. Acquiring a VIN number for a vehicle usually involves little more than looking for it on the dashboard underneath the windshield.
In addition, the researchers discovered that it was also possible to send commands to the climate control system remotely: the server could be instructed to turn on, or turn off, the heating or air conditioning on any Leaf that uses NissanConnect. While the climate control is programmed to turn itself off after 15 minutes when the car is unplugged, there’s nothing stopping the API from sending multiple commands over and over. Hypothetically, you could park your car somewhere, and come back several hours later to a blasting A/C and a nearly dead battery. The app doesn’t provide control over locks, engine, steering, or anything else that would generally be classified as safety critical, but it’s still a fairly serious security issue.
What’s weird about this, as Hunt discovered, is not so much that the Nissan app had poor security: it’s more that the security was utterly nonexistent, to the extent that Hunt and his colleagues think it must have been a conscious choice by Nissan. According to them, building an API like this “is just nuts.”
More than a month after Hunt first contacted Nissan about this issue (but just a day after Hunt put up his blog post), the company disabled the NissanConnect app and put out this statement:
“The NissanConnect EV app is currently unavailable. This follows information from an independent IT consultant and subsequent internal Nissan investigation that found the dedicated server for the app had an issue that enabled the temperature control and other telematics functions to be accessible via a non-secure route.
No other critical driving elements of the Nissan LEAF or eNV200 are affected... The only functions that are affected are those controlled via the mobile phone—all of which are still available to be used manually, as with any standard vehicle.
We're looking forward to launching updated versions of our apps very soon."
Evan Ackerman is a senior editor at IEEE Spectrum. Since 2007, he has written over 6,000 articles on robotics and technology. He has a degree in Martian geology and is excellent at playing bagpipes.