Millions of Volkswagen cars could in principle be unlocked from a distance by hackers, according to a new report. It’s one more strike against a German company that’s had more than its share of bad news, what with VW’s admitted cheating on diesel-emissions tests.
But there’s plenty of bad news to go around: The report notes that many models from other companies have vulnerabilities of their own. And the problem is worse with older cars, designed before carmakers gave much thought to cybersecurity.
Flavio D. Garci, David Oswald, and Pierre Pavlidès at Britain’s University of Birmingham wrote the report, together with Timo Kasper of Kasper & Oswald, a German security firm. They released it [PDF] last week at the 25th USENIX Security Symposium, in Austin, Texas.
Kasper told the BBC that the researchers informed Volkswagen of the vulnerability in late 2015 and that the company was taking steps to mitigate the problem. But he said there are “at least 10 more, very widespread” vulnerabilities affecting other car brands, which the researchers won’t publish until the manufacturers have had time to do something about them.
The report found two weaknesses. The simpler hack involves discovering which of VW’s small handful of “master key” codes is used by a particular remote key fob by eavesdropping on a single signal from that fob to its car. That code, together with the algorithm, can then be used to unlock that car. A lot of cars are involved: The VW Group sold about 100 million cars from 2002 until 2015, and the researchers estimate that “the vast majority is vulnerable to the attacks presented” in their study.
The more complex hack allows the bad guys to take over cars using the Hitag2 rolling code method, used in cars made by Chevrolet, Renault, and Ford,
among others. Rolling code changes with each use, but the algorithm that changes it can be inferred “with four to eight rolling codes and a few minutes of computation on a laptop,” the researchers write.
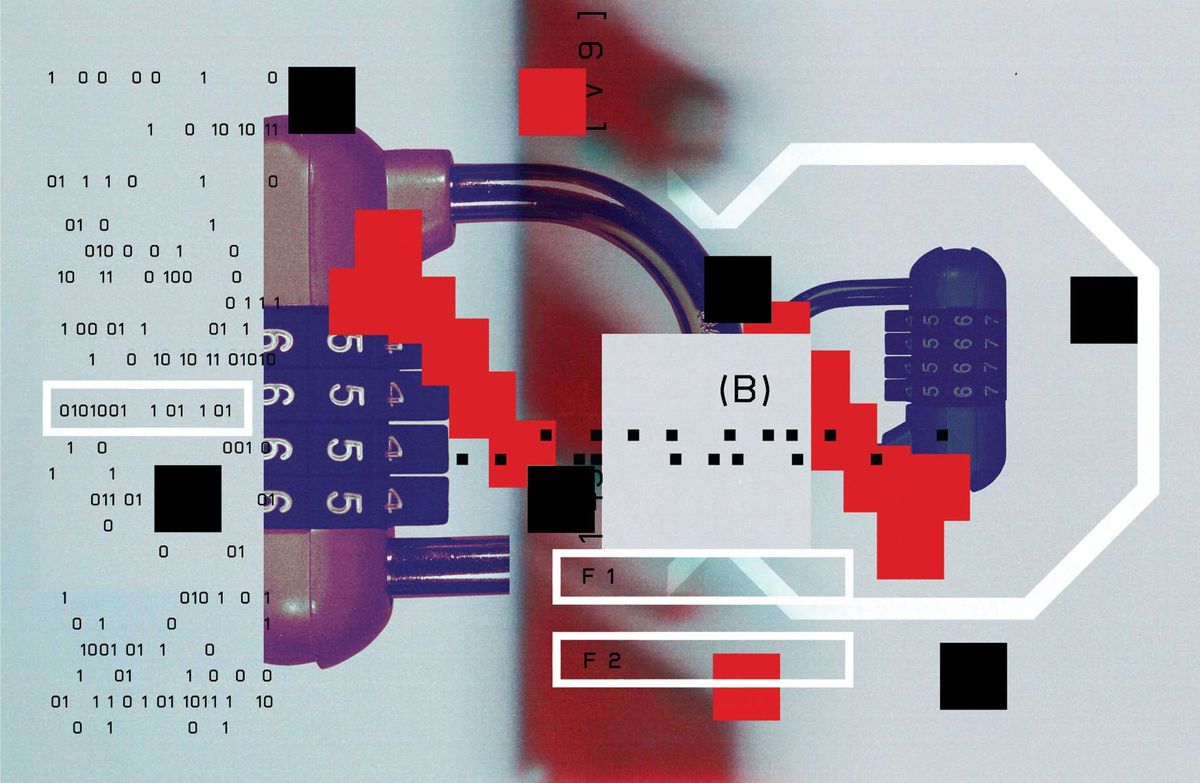
The paper shows a picture of the researchers’ handmade RF transceiver, which is basically an Arduino processor and a few other parts, all fitting on a circuit board hardly larger than the battery to which it is attached. “Our simple setup... costs ≈ $40,” the paper continues, “is battery-powered, can eavesdrop and record rolling codes, emulate a key, and perform reactive jamming.”
The main challenge to the would-be hacker is in getting a number of distinct rolling codes, though there’s no need that they all be consecutive codes. But the researchers helpfully note that it should be easy to induce the naive car owner into giving up that information by punching his remote fob again and again.
“The adversary could selectively jam the signal during the final checksum byte (which is predictable),” they write, referring to the data at the end of a transmission. “In this case, the vehicle ignores the rolling code, but the adversary nevertheless obtains the keystream. The victim would hence notice that the vehicle does not respond, and instinctively press the button repeatedly. After having received the fourth signal, the adversary stops jamming and the remote control operates normally from the victim’s point of view.”
How might bad guys use this trick to do evil? The authors note that they could take something out of the car or put something (or someone) into it, perhaps giving the owner a nasty surprise later, when he’s all alone on the open road. And of course once inside a parked car the hacker would have the safety and leisure to continue the break-in with tools applied directly to the electronic systems under the dashboard.
The remote fob has been a security bugbear for years, though the focus of worry keeps on changing. In 2014 IEEE Spectrum reported that thieves were making clones of fobs they’d “borrowed” while a car was in the shop, being repaired. But that takes planning and, perhaps, accomplices. If you can get what you want with a homemade circuit board, you are better able to keep the secret—and all the loot.
Philip E. Ross is a senior editor at IEEE Spectrum. His interests include transportation, energy storage, AI, and the economic aspects of technology. He has a master's degree in international affairs from Columbia University and another, in journalism, from the University of Michigan.