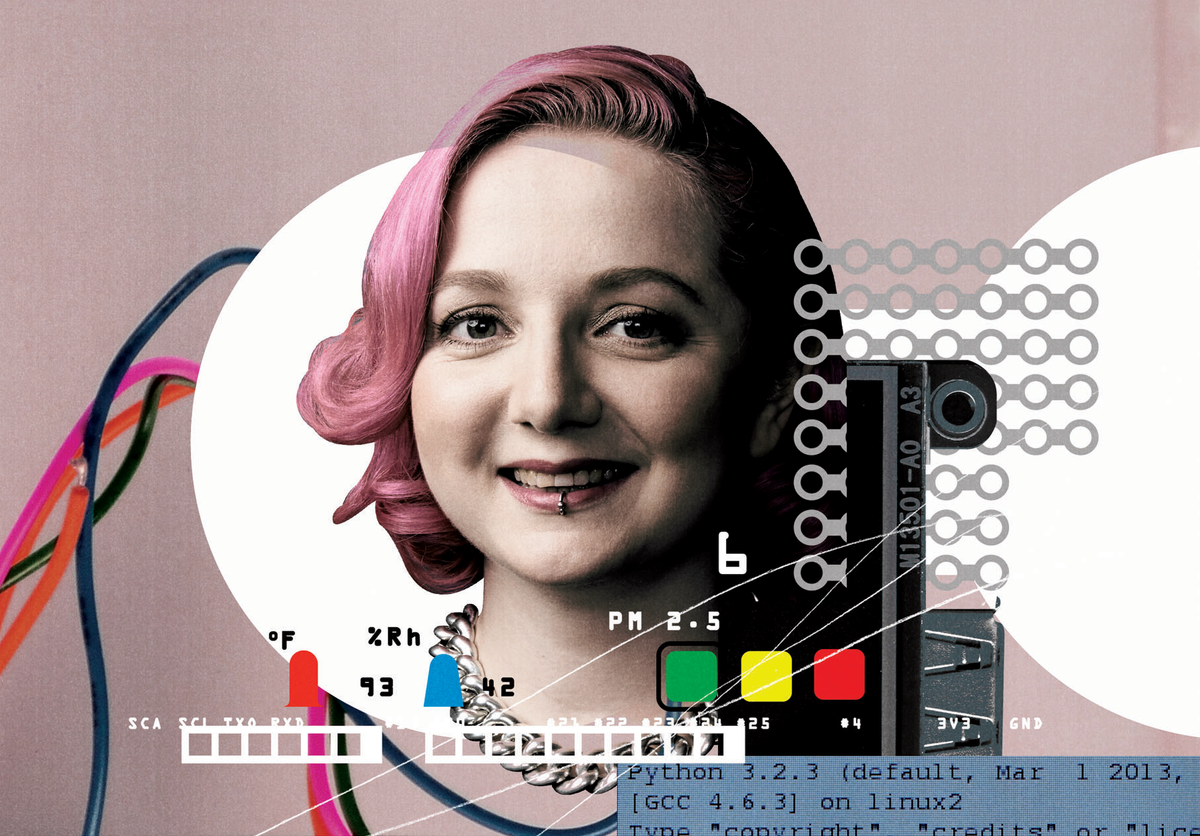
Photo: Iris van Herpen
What makes this outfit, which made its debut at Iris van Herpen’s Paris Fashion Week show in January, different from most frocks? The designer collaborated with experts from the MIT Media Lab and Materialise, the Belgian company specializing in software for additive manufacturing. Stratasys, a leading 3-D printing firm, handled the fabrication end of the production. The company was able to build in texture and stretchability using Materialise’s technique for combining hard and soft materials into a single printing.







Willie Jones
Willie Jones is an associate editor at IEEE Spectrum. In addition to editing and planning daily coverage, he manages several of Spectrum's newsletters and contributes regularly to the monthly Big Picture section that appears in the print edition.
The Conversation (0)