General Motors has created the job of product security chief and filled it with Jeffrey Massimilla, who'd already been working for the company's infotainment business.
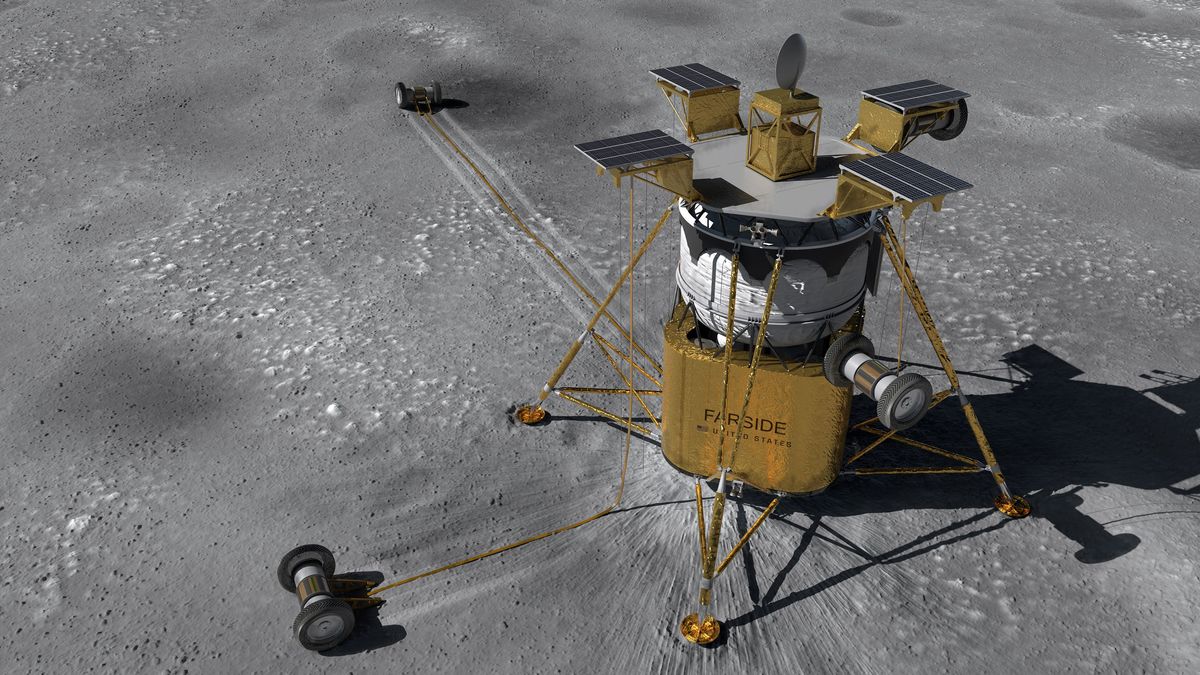
It's part of a trend: automakers and the people planning tomorrow's smart roads are worried that connected vehicles might present a fat, juicy target to hackers and malware. Ford Motor Company, for instance, recently ran help-wanted ads for cybersecurity experts. It's all because of many emerging vulnerable points that a hacker might use to get into a car's electronic guts.
"With connectivity comes responsibility," said Roger Berg, vice president for wireless technologies at Denso, in a talk at the ITS World Conference two weeks ago, in Detroit. "It opens you to attack." At the conference Denso, a Japanese auto supplier, demonstrated a system for cars to talk to other cars.
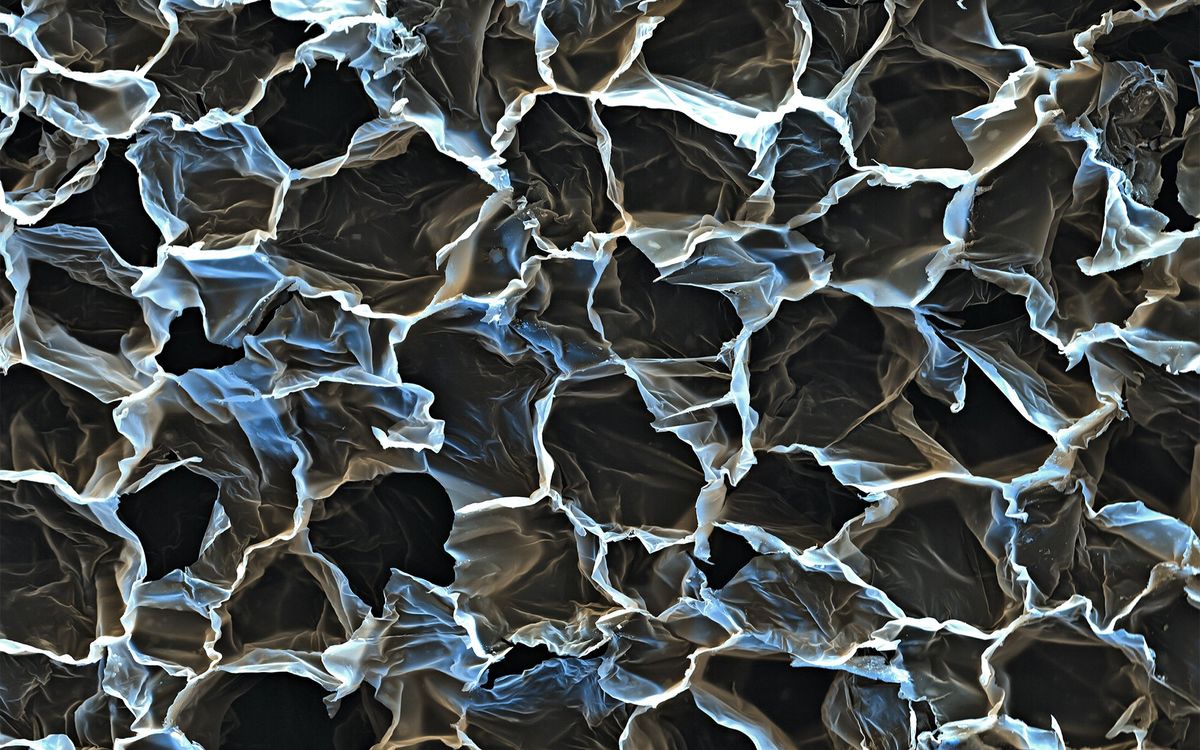
It's easy to give a car yet another link to the outside world, but hard to knit them all together securely. And today's cars offer a lot of links—WiFi, 4G, infotainment, GPS, services accessed through the cloud, even manufacturer-issued software updates. And once a bad guy or a bit of malware gets into one part of a car, it might penetrate to others, maybe even to the driver's phone.
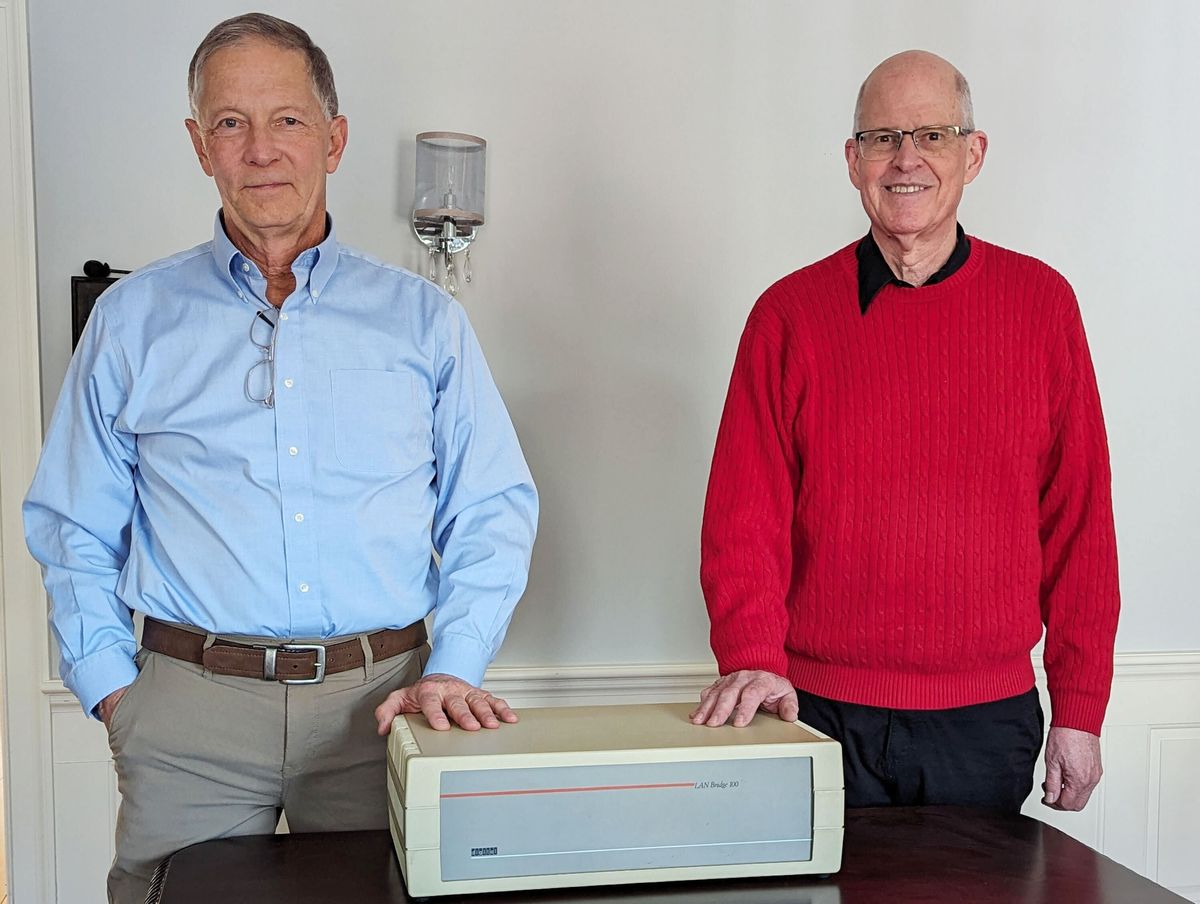
It seems like a rolling rerun of how corporate computing lost its innocence in the 1960s and early 1970s. That's when administrators of mainframes hosting hundreds of accounts finally, and grudgingly, began installing password protection after dastardly people began stealing computer time from other people. At Northwestern University passwords were instituted in the mid-1970s after someone who called himself Robin Hood effortlessly impersonated professors with big computer budgets.
Password protection is probably not the way for cars, though. You can get into all sorts of trouble trying to type in multiple, dimly remembered passwords so that your car will finally turn off the windshield wipers.
Philip E. Ross is a senior editor at IEEE Spectrum. His interests include transportation, energy storage, AI, and the economic aspects of technology. He has a master's degree in international affairs from Columbia University and another, in journalism, from the University of Michigan.