According to new research, chip-based “Smartcard” credit and debit cards—the next-generation replacement for magnetic stripe cards—are vulnerable to unanticipated hacks and financial fraud. Stricter security measures are needed, the researchers say, as well as increased awareness of changing terms-of-service that could make consumers bear more of the financial brunt for their hacked cards.
The work is being presented at this week’s Black Hat 2014 digital security conference in Las Vegas. Ross Anderson, professor of security engineering at Cambridge University, and co-authors have been studying the so-called Europay-Mastercard-Visa (EMV) security protocols behind emerging Smartcard systems.
Though the chip-based EMV technology is only now being rolled out in North America, India, and elsewhere, it has been in use since 2003 in the UK and in more recent years across continental Europe as well. The history of EMV hacks and financial fraud in Europe, Anderson says, paints not nearly as rosy a picture of the technology as its promoters may claim.
“The idea behind EMV is simple enough: The card is authenticated by a chip that is much more difficult to forge than the magnetic strip,” Anderson and co-author Steven Murdoch wrote in June in the Communications of the ACM [PDF]. “The card-holder may be identified by a signature as before, or by a PIN… The U.S. scheme is a mixture, with some banks issuing chip-and-PIN cards and others going down the signature route. We may therefore be about to see a large natural experiment as to whether it is better to authenticate transactions with a signature or a PIN. The key question will be, “Better for whom?””
Neither is ideal, Anderson says. But signature-based authentication does put a shared burden of security on both bank and consumer and thus may be a fairer standard for consumers to urge their banks to adopt.
“Any forged signature will likely be shown to be a forgery by later expert examination,” Anderson wrote in his ACM article. “In contrast, if the correct PIN was entered the fraud victim is left in the impossible position of having to prove that he did not negligently disclose it.”
And PIN authentication schemes, Anderson says, have a number of already discovered vulnerabilities, a few of which can be scaled up by professional crooks into substantial digital heists.
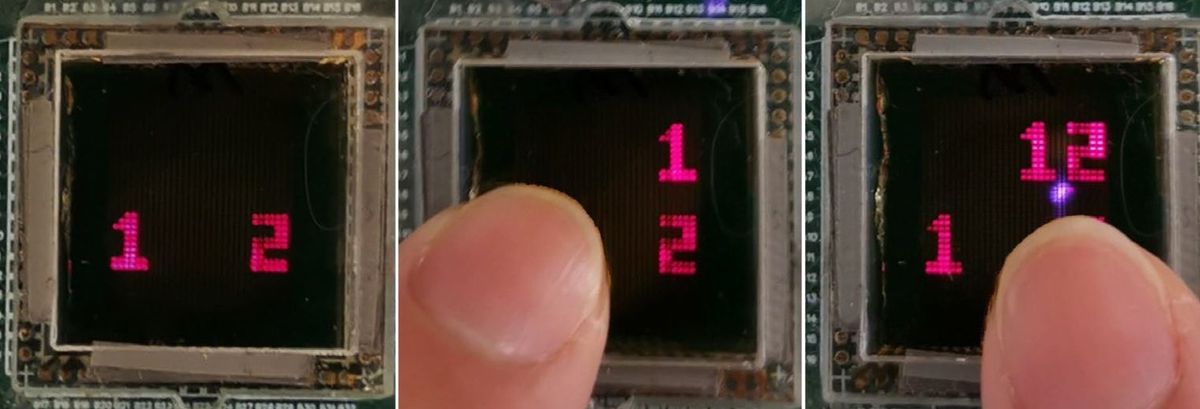
In May, Anderson and four colleagues presented a paper at the IEEE Symposium on Security and Privacy on what they called a “chip and skim” (PIN-based) attack. This attack takes advantage of some ATMs and credit card payment stations at stores that unfortunately take shortcuts in customer security: The EMV protocol requires ATMs and point-of-sale terminals to broadcast a random number back to the card as an ID for the coming transaction. The problem is many terminals and ATMs in countries where Smartcards are already used issue lazy “random” numbers generated by things like counters, timestamps, and simple homespun algorithms that are easily hacked.
As a result, a customer can—just in buying something at one of these less-than-diligent stores or using one of these corner-cutting ATMs—fall prey to an attack that nearby criminals could set up. The attack would allow them to “clone” a customer’s Smartcard and then buy things on the sly with the compromised card. Worse still, some banks’ terms and conditions rate card cloning—which EMV theoretically has eliminated—as the customer’s own fault. So this sort of theft might leave an innocent victim with no recourse and no way of refunding their loss.
“At present, if you dispute a charge, the bank reverses it back to the merchant,” Anderson says. “Merchants are too dispersed to go after customers much. But EMV shifts the liability to the bank, and the banks in anticipation are rewriting their terms and conditions so they can blame the customer if they feel you might have been negligent. I suggest you check out your own bank's terms and conditions.”
Margo Anderson is the news manager at IEEE Spectrum. She has a bachelor’s degree in physics and a master’s degree in astrophysics.