Last week, the U.S. Court of Appeals of the 11th Circuit in Atlanta ruled (pdf) that a person under investigation in a child-pornography case could not be forced to produce the unencrypted contents of the hard drives on his lap top or the information contained on five external hard drives.
According to the Appeals Court ruling, and a Wall Street Journal article about the case from last Friday, the person was subpoenaed by a Northern District of Florida grand jury and ordered to produce the unencrypted contents of all the hard drives. The person refused, and invoked his Fifth Amendment constitutional privilege against self-incrimination.
The US Attorney, as the law allows, got a district court order demanding that the defendant provide the information under the "public interest" clause of the U.S. Codes; however, the U.S. government also had to grant the person immunity from prosecution. As the Court explained in its ruling, when the government grants immunity in this situation:
"... the witness may not refuse to comply with the order on the basis of his privilege against self-incrimination; but no testimony or other information compelled under the order (or any information directly or indirectly derived from such testimony or other information) may be used against the witness in any criminal case, except a prosecution for perjury, giving a false statement, or otherwise failing to comply with the order."
But the U.S. Attorney had sought a different outcome, asking a district court to provide immunity only with regard to the defendant's act of production of the unencrypted contents, and not the contents themselves. In other words, the U.S. Attorney wanted to ensure that the "immunity would not extend to the Government’s derivative use of contents of the drives as evidence against him in a criminal prosecution," the appeals court said in its ruling.
The person, not surprisingly, still refused to decrypt the drives. He maintained that he'd forgotten the passwords and that even if he could remember them, using them to decrypt the files would violate his Fifth Amendment rights. The district court didn't buy either reason; it held him in contempt of court and ordered him jailed. The district court reasoned that forcing the person to provide the passwords would not constitute testimony against himself. Moreover, it concluded that the government's request for limited immunity was within its rights. The person immediately appealed the ruling.
The Appeals Court found that the district court had "erred in two respects... it erred in concluding that [the person's] act of decryption and production would not constitute testimony...[and] in limiting his immunity..."
One of the reasons the Appeal Court found in the person's favor was, as the WSJ states, the Fifth Amendment "protects testimony in which a person is forced to use the 'contents of his own mind' to state a fact, in this case, the encryption passwords."
Another was that, in this case, the government had no proof that anything of a criminal nature was on the encrypted drives. If indeed the government already had proof, the evidence would be considered a "foregone conclusion" and as a result, the Fifth Amendment wouldn't hold. The WSJ noted that, "a federal court in Vermont in 2009 ordered a suspect to produce an unencrypted version of a drive on his laptop based on that legal wrinkle because authorities had already seen evidence of child pornography on it."
All that it seems pretty clear, even to my non-legally-trained mind. But the legal hairsplitting doesn't end there. At about the same time in Colorado, a woman being charged with real estate fraud was ordered by a Denver Federal District Court to turn the encryption passwords to her laptop over to the FBI today or face possible contempt charges. Her appeal to the Tenth Circuit Court of Appeals was denied.
The WSJ, in an article appearing today, noted that the Denver District Court denied the appeal because the suspect "in effect already had been incriminated because the government already had solid evidence she was the sole or primary user of the laptop, and thus would not gain additional, incriminating evidence by compelling her to decrypt it." What isn't clear from the article is whether the government had already seen evidence of fraud on her laptop (i.e., in the unencrypted part), or whether the government merely had evidence of fraud in general. If it is only the latter, I would be surprised if her lawyers don't appeal to the U.S. Supreme Court for clarification given the 11th Circuit's reasoning (unless I am missing something).
Just as in the recent GPS tracking case, I have little doubt that the US Supreme Court will sooner or later make a somewhat definitive ruling about when a person can be ordered to provide encryption passwords to their electronic devices.
If a future ruling overturns the 11th Circuit Court of Appeals' reasoning, then it may have major implications also for travelers. Currently, US Customs and Border Protection can legally (pdf) seize and copy the information from any electronic device brought into the US and get help to read such information; if it finds anything illegal on those devices, it can also file charges against the person possessing the device. However, Customs cannot force a person to provide the encryption passwords to their devices, at least not yet. This could change if the 11th Circuit ruling is itself overturned.
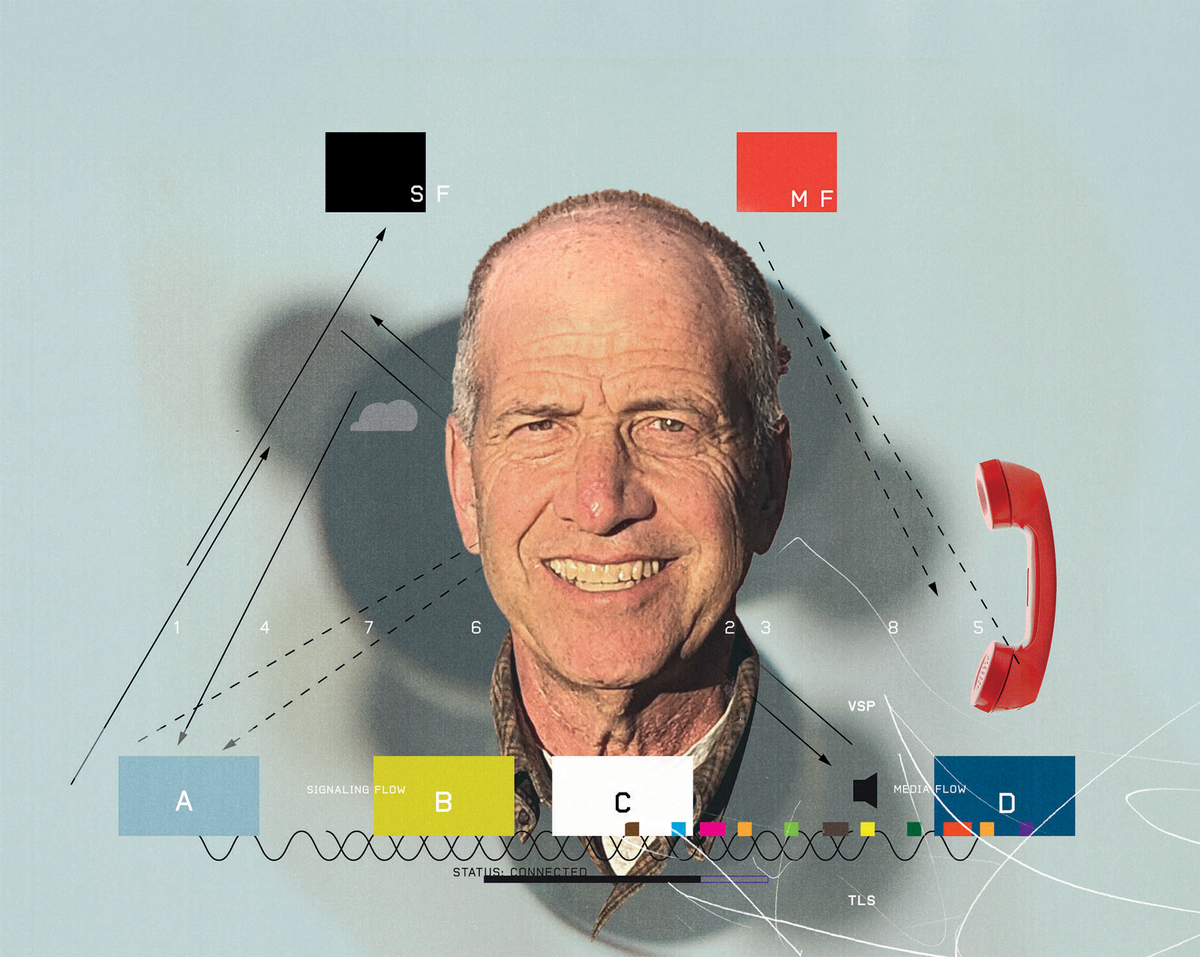
Robert N. Charette is a Contributing Editor to IEEE Spectrum and an acknowledged international authority on information technology and systems risk management. A self-described “risk ecologist,” he is interested in the intersections of business, political, technological, and societal risks. Charette is an award-winning author of multiple books and numerous articles on the subjects of risk management, project and program management, innovation, and entrepreneurship. A Life Senior Member of the IEEE, Charette was a recipient of the IEEE Computer Society’s Golden Core Award in 2008.